We like to create new Microsoft Entra ID users in the company. Going through the…
Enable Azure MFA number matching for extra security
Every organization knows that security is essential and needs to be solid. Nowadays, every organization enables MFA and thinks that they are protected and done. Well, hold your horses because that’s not the case. What if a user gets an MFA prompt and accidentally accepts it when clicking on it? That’s when number matching in Azure AD plays a role and makes MFA push notifications more secure. In this article, you will learn how to enable MFA number matching in Microsoft Authenticator app for sign-in security purposes.
Table of contents
Enable Azure MFA
Configuring MFA in Azure/Microsoft 365 is a prerequisite, and there are two methods:
Note: It’s recommended to configure Azure AD Multi-Factor Authentication instead of per-user MFA.
Azure MFA number matching
Require number matching for push notifications is a feature in Azure AD. It presents users with a number when they respond to an MFA push notification using the Authenticator app. They need to type that number into the app to complete the approval.
Note: Number matching in Azure AD is flexible and can be targeted to a single user, multiple users, all users, and groups.
Note: Microsoft will enable Azure MFA number matching by default for all tenants from May 8, 2023.
Let’s look at how to configure MFA number matching and how it looks.
Enable Azure MFA number matching
To enable number matching in Azure AD, follow these steps:
Step 1. Sign in to Microsoft Azure Portal.
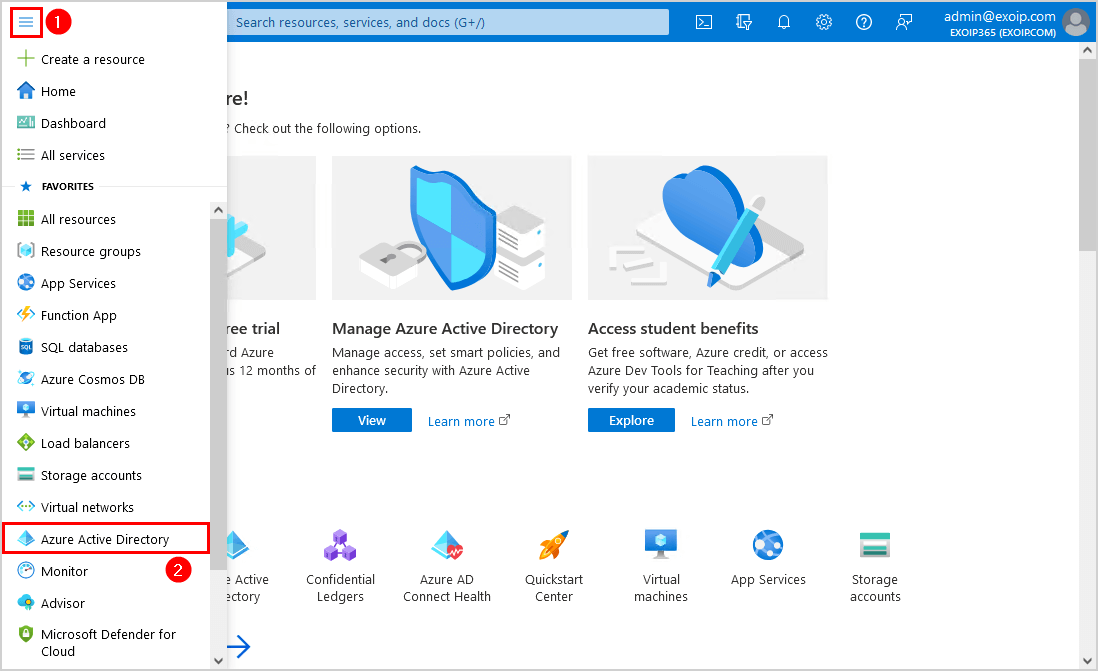
Step 2. Click on Menu > Azure Active Directory.
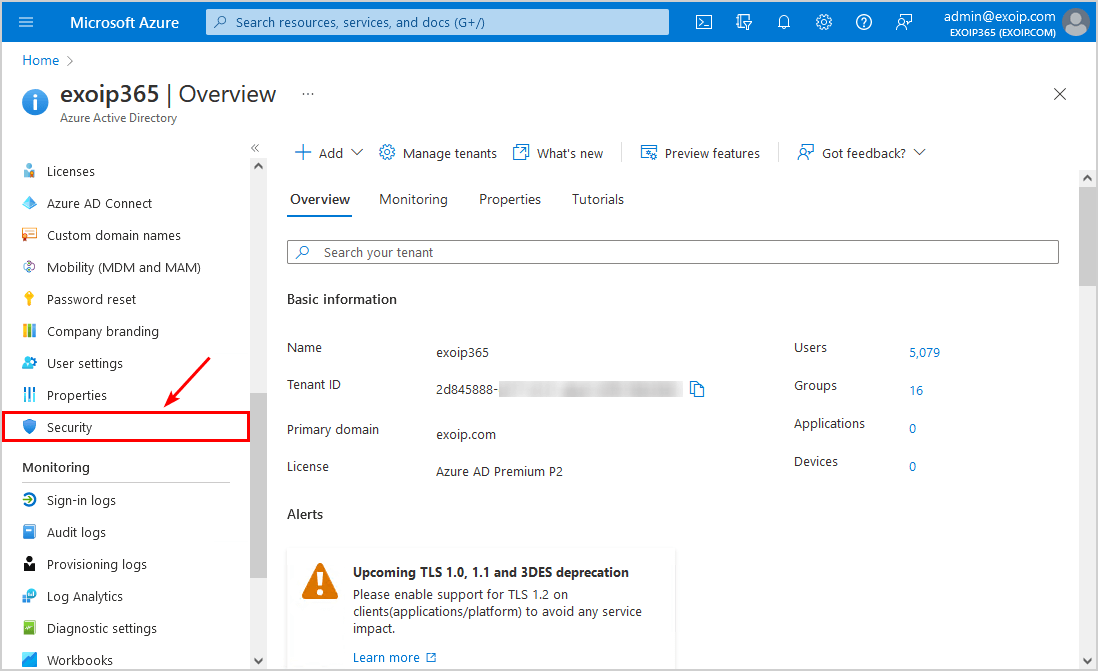
Step 3. Click on Security.
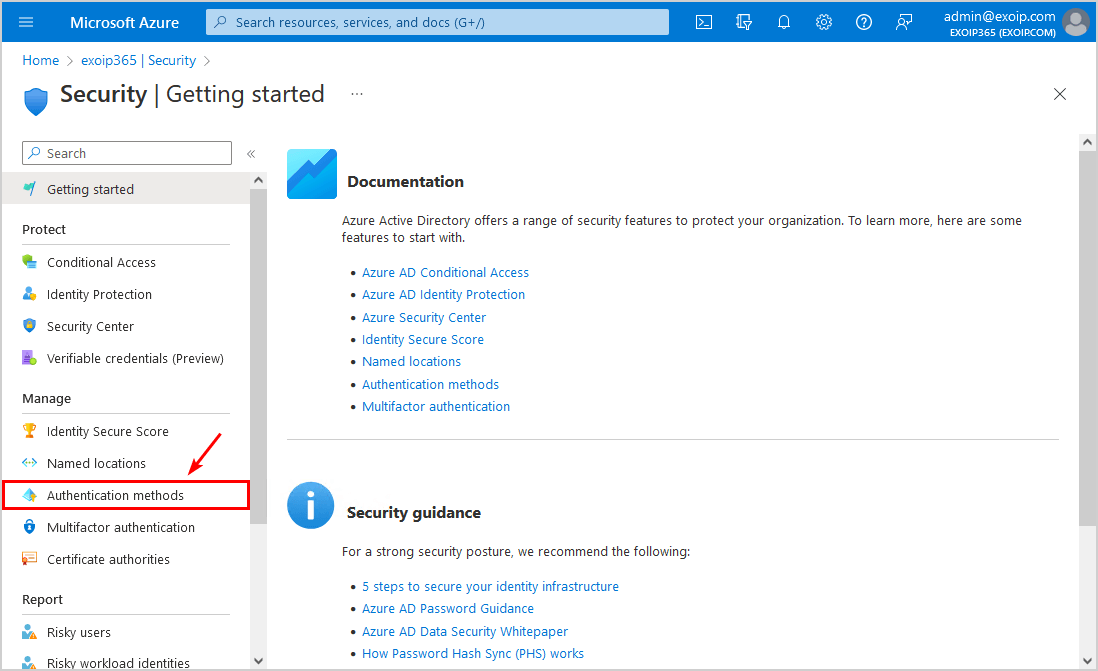
Step 4. Click on Authentication methods.
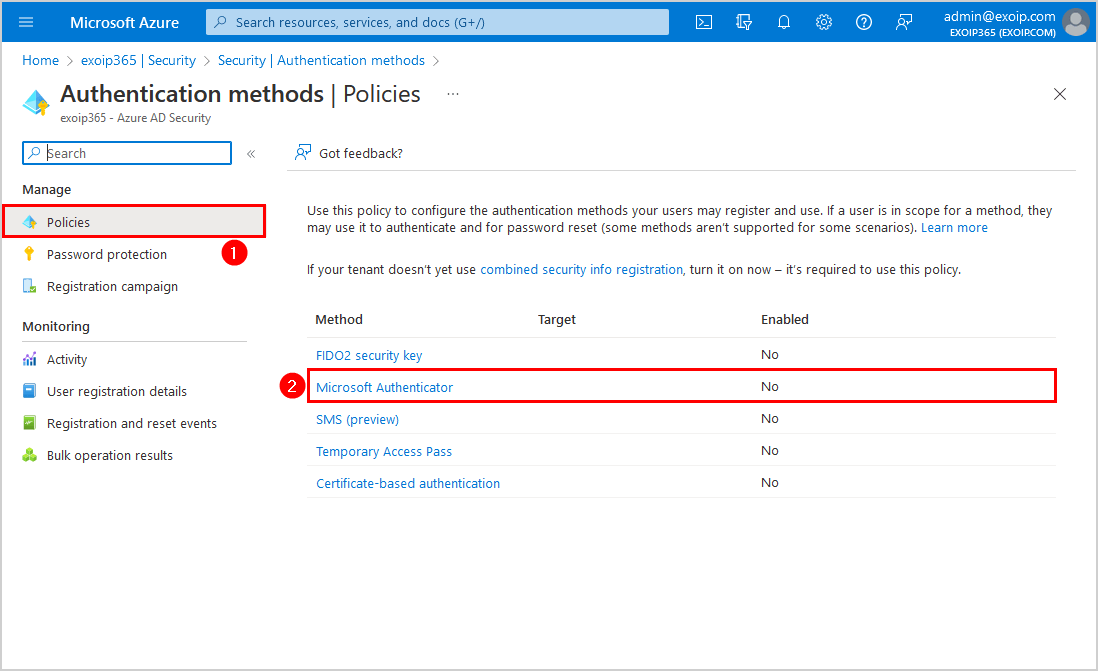
Step 5. Click on Policies > Microsoft Authenticator.
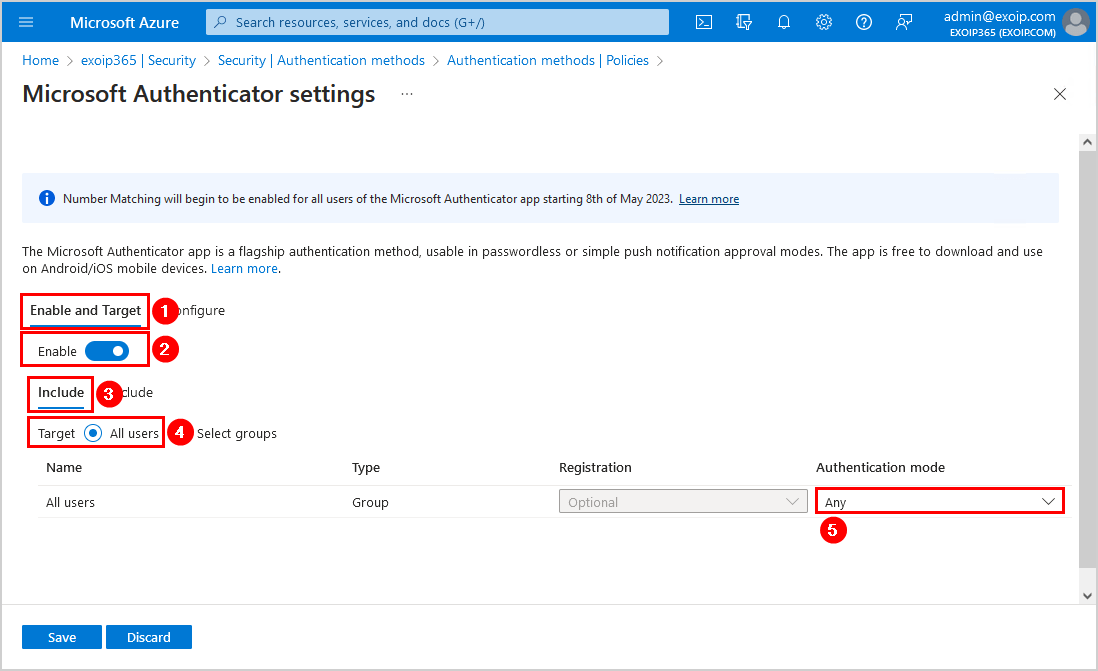
Step 6. Click on the Enable and Target tab and configure the below settings:
- Enable: Yes
- Include > Target: All users
- Authentication mode: Any
Suppose you want to enable it on a group or a test account; click Select users and select the users/groups.
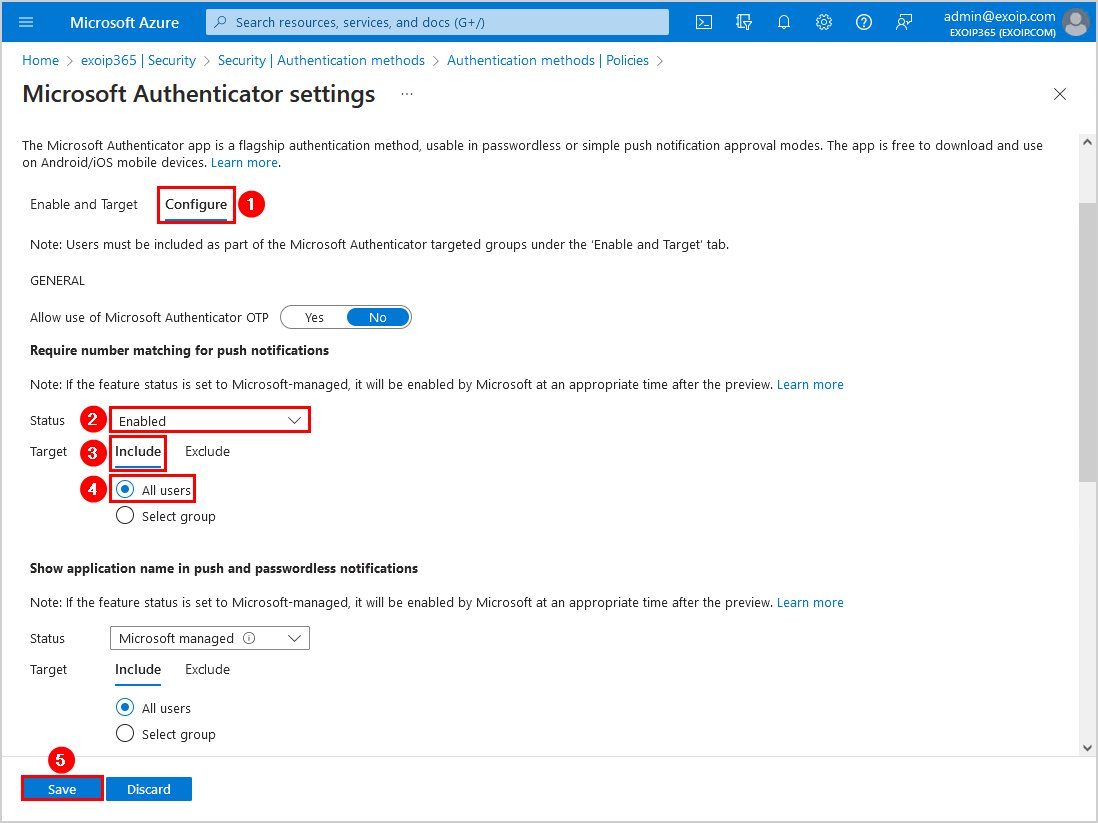
Step 7. Click on the Configure tab and configure the below settings for Require number matching for push notifications. Don’t forget to Save.
- Status: Enabled
- Target: Include – All users
Note: Two more features are available on the Microsoft Authenticator settings configure page. You should enable these features for security improvements. Read more in Enable Azure MFA application name and Enable Azure MFA geographic location.
Step 8. Confirm that Microsoft Authenticator shows the target that you have set and the status enabled.
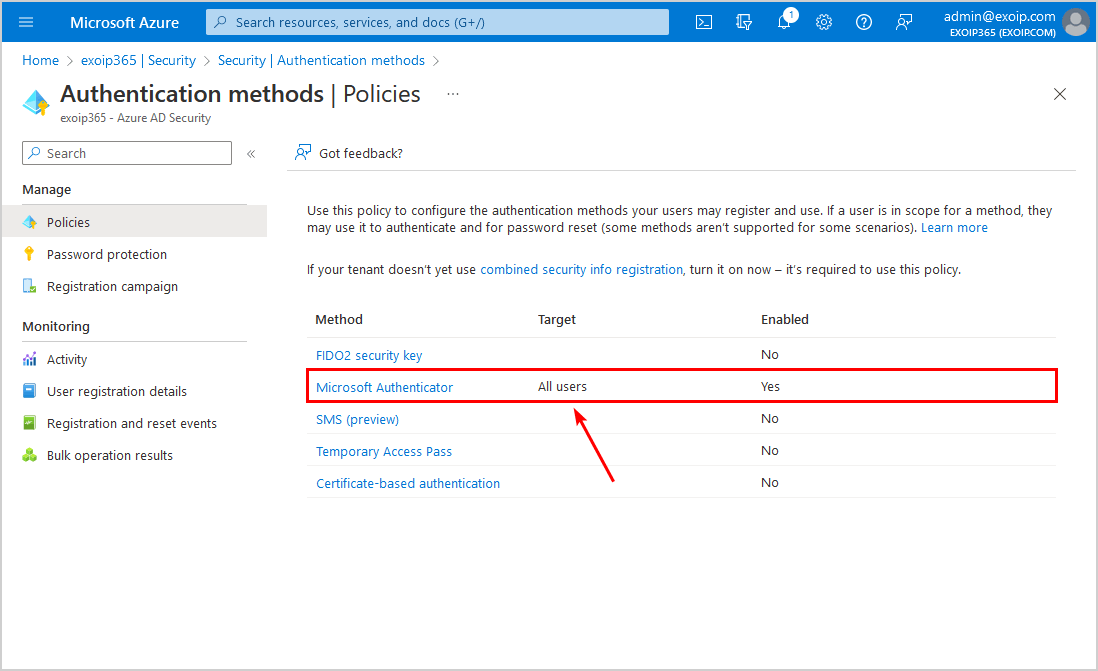
In the next step, you will test that everything works as you expect.
Verify Azure MFA number matching
To test that Azure MFA number matching works, follow the below steps:
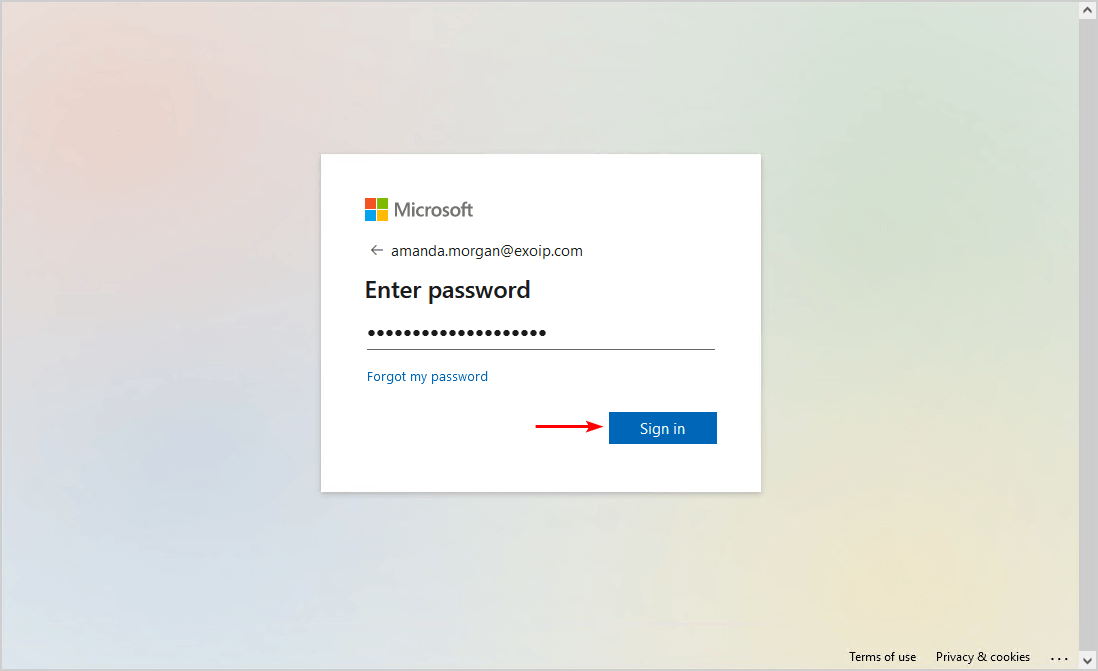
Sign in to Microsoft 365 portal.
Note: You need to have MFA enabled on the account you like to test and not sign in from a network that is excluded from MFA.
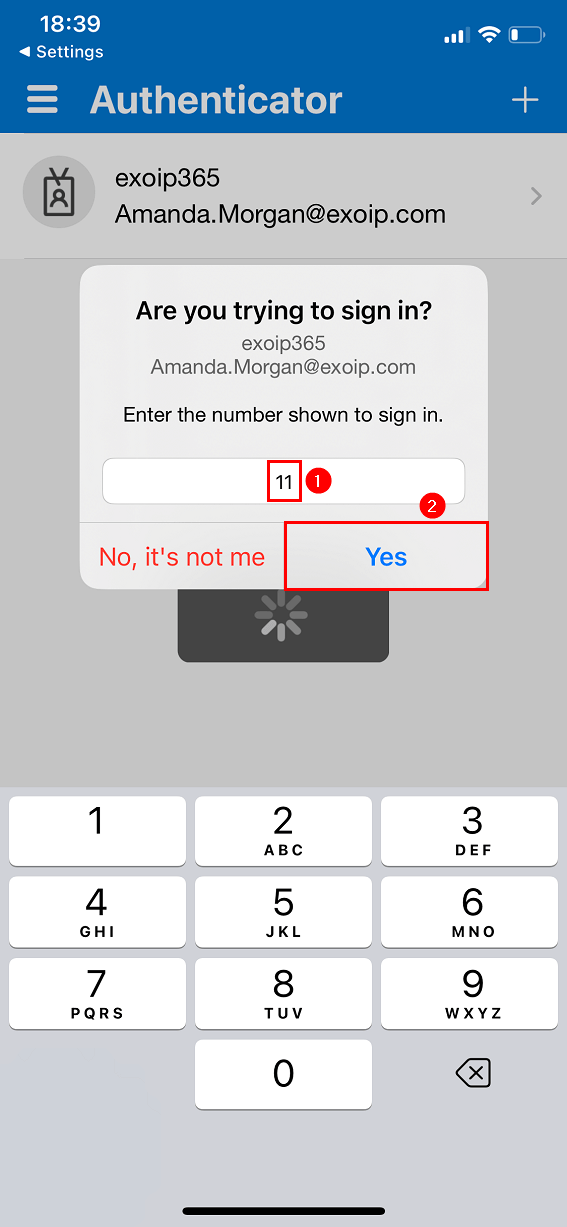
The approve sign in request message appears with a randomly generated number.
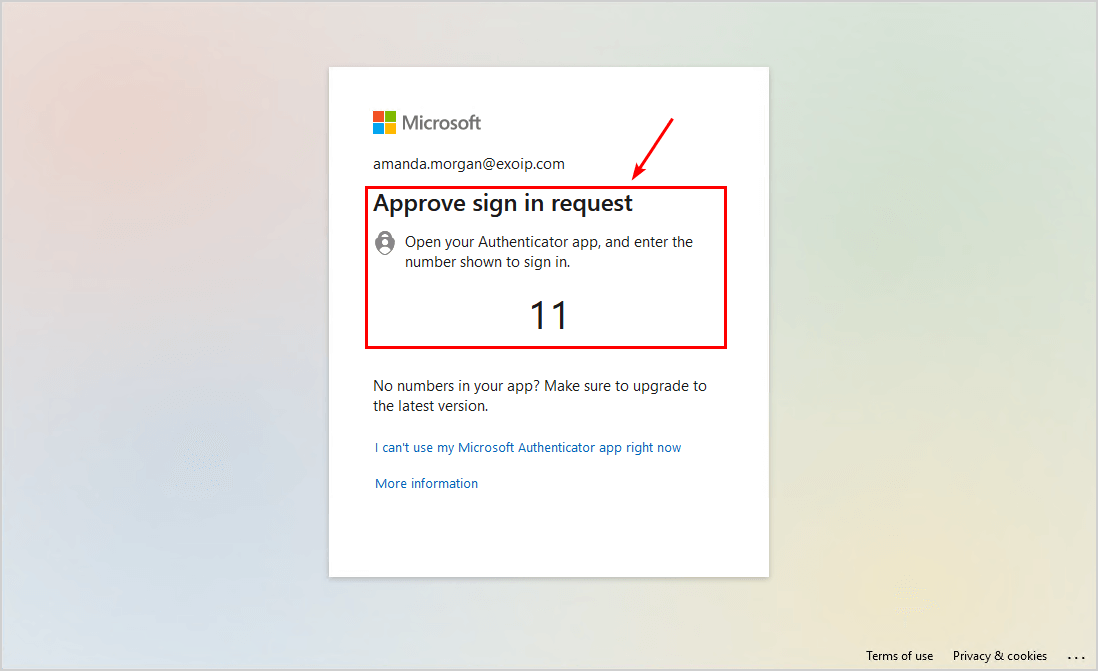
Enter the number in the Microsoft Authenticator app to sign in. Next, tap Yes.
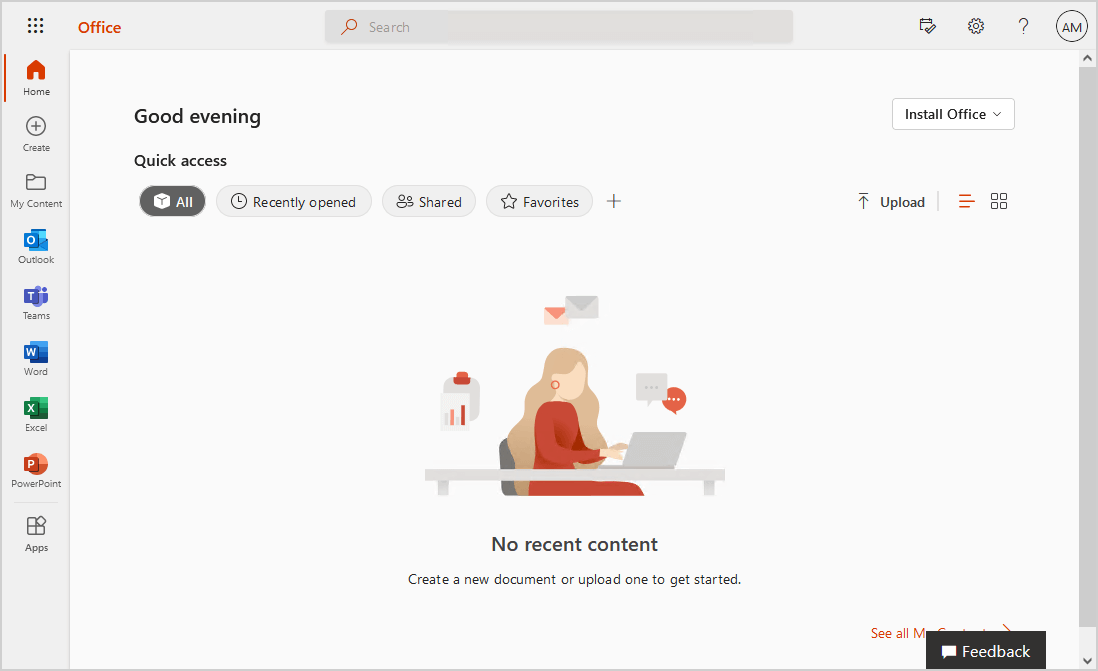
You will successfully sign in to the portal.
That’s it! You successfully did configure MFA number matching in Azure AD for the users.
Read more: Enable MFA Office 365 with PowerShell »
Conclusion
You learned how to enable Azure MFA number matching and improve sign-in security. It’s essential to enable the feature for all users. You can first select a group and see how they deal with it so you can update the documentation before you send it to the users and enable it for all the users.
Did you enjoy this article? You may also like Move from per-user MFA to Conditional Access MFA. Don’t forget to follow us and share this article.


Great doc!
This feature is going to be enabled for all MS users whether they like it or not on May 08, 2023 anyway. So, getting a head start.
Thanks!
Hi,
The problem is when you use MFA with CAL and it s not configured on a tenant level you don t have access to the matching number option 🙁