Companies like to know how many emails they get an hour or a day. Perhaps…
Enable MFA Office 365 with PowerShell
We need to enable MFA for Office 365 users for extra security. What is the fastest and safest way to enable Office 365 MFA? In this article, you will learn how to enable MFA Office 365 for all users and one user with PowerShell.
Table of contents
Why enable Microsoft 365 MFA?
There are a couple of reasons why you need to enable Microsoft 365 MFA:
- Secure environment from attacks
- Move from another MFA vendor
Note: Do you have Azure AD Premium plan 1 or 2? We recommend you configure Azure AD Multi-Factor Authentication instead of per-user MFA (this article).
How to enable per-user MFA Office 365 with PowerShell
To enable per-user MFA in Microsoft 365/Office 365 with PowerShell, go through the below steps:
Connect to Azure AD PowerShell
Start Windows PowerShell and connect to Azure AD PowerShell.
Connect-MsolServiceEnable MFA Office 365 for single user
Enable MFA for a single Office 365 user.
$mf= New-Object -TypeName Microsoft.Online.Administration.StrongAuthenticationRequirement
$mf.RelyingParty = "*"
$mfa = @($mf)
Set-MsolUser -UserPrincipalName "Amanda.Morgan@exoip.com" -StrongAuthenticationRequirements $mfaEnable MFA Office 365 for all users
Enable MFA for all Office 365 users.
$mf= New-Object -TypeName Microsoft.Online.Administration.StrongAuthenticationRequirement
$mf.RelyingParty = "*"
$mfa = @($mf)
Get-MsolUser -All | Set-MsolUser -StrongAuthenticationRequirements $mfaEnable MFA Office 365 in Azure/Microsoft 365 portal
Suppose you want to use something other than PowerShell to enable per-user MFA for a single or all users. Another way is to use the portal and configure per-user MFA in Microsoft 365/Azure.
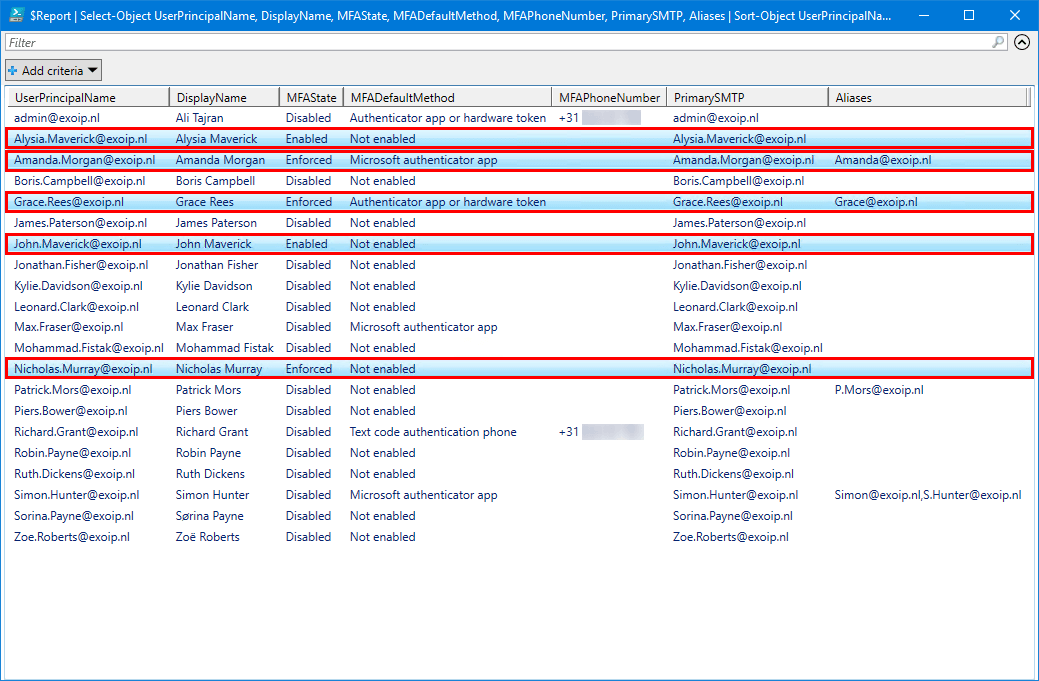
Export Office 365 MFA status
Do you like to check the Office 365 MFA status and verify that MFA for the users is successfully enabled? An excellent way is to export Office 365 users MFA status report with PowerShell.
That’s it!
Important: Always use MFA to protect the accounts from attacks and compromised passwords. It adds another layer of protection that helps organizations.
Read more: Disable MFA Office 365 with PowerShell »
Conclusion
You learned how to enable MFA Office 365 with PowerShell. Connect to Azure AD with PowerShell and run the command to enable MFA for all Office 365 users or single user. Don’t forget to always use MFA for extra protection.
Did you enjoy this article? You may also like Move from per-user MFA to Conditional Access MFA. Don’t forget to follow us and share this article.

This is something I want to run right now, but I think the code is old. I am getting errors. I can’t use Connect-MsolService anymore, I think.
Is there a version of this for per user mfa in azure?
Thanks
The PS commands still work (I just tried them).
These PowerShell commands are for per-user MFA in Azure AD/Microsoft 365 admin center.
How to turn it off?
Read the article: Disable MFA Office 365 with PowerShell.