There is a difference when you want to uninstall the last Exchange Server on-premises or…
ISP blocks SMTP port 25 – Bypass/Fix
Outgoing mail stays in the Exchange Server mail queue and is not delivered. What’s going on? The incoming mail flows, but outgoing mail doesn’t. The mail needs to flow to the outside world, and we can’t have this delay. Let’s look at why the outgoing messages stay in the mail queue and the solution.
Table of contents
Get mail queue last error
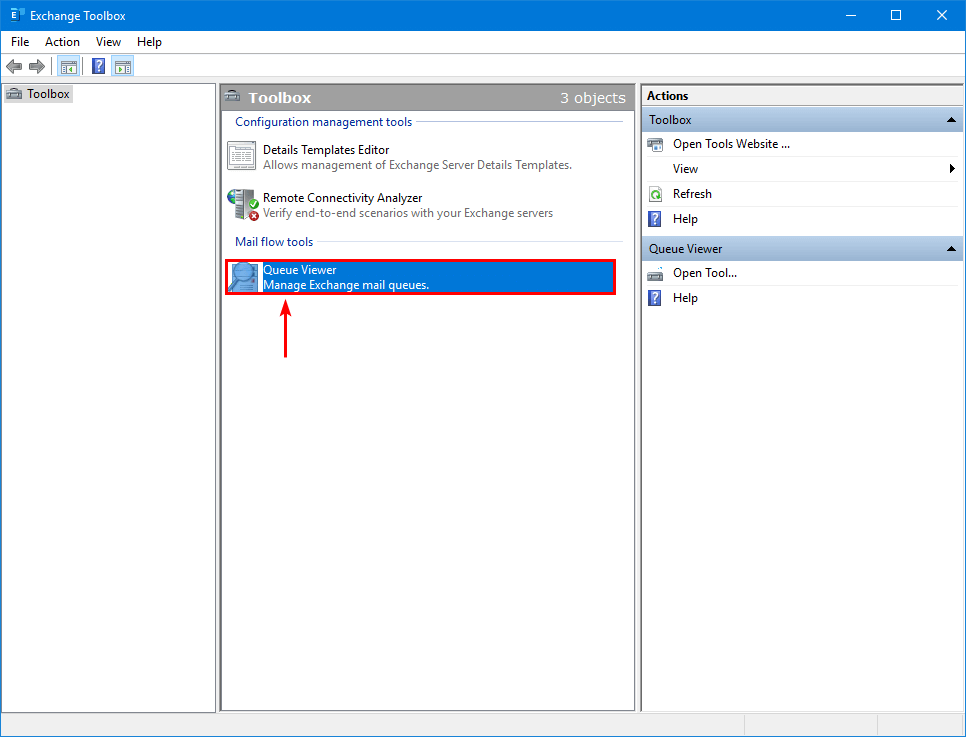
The first step is to check the messages stuck in the queue. Start Exchange Toolbox > Queue Viewer.
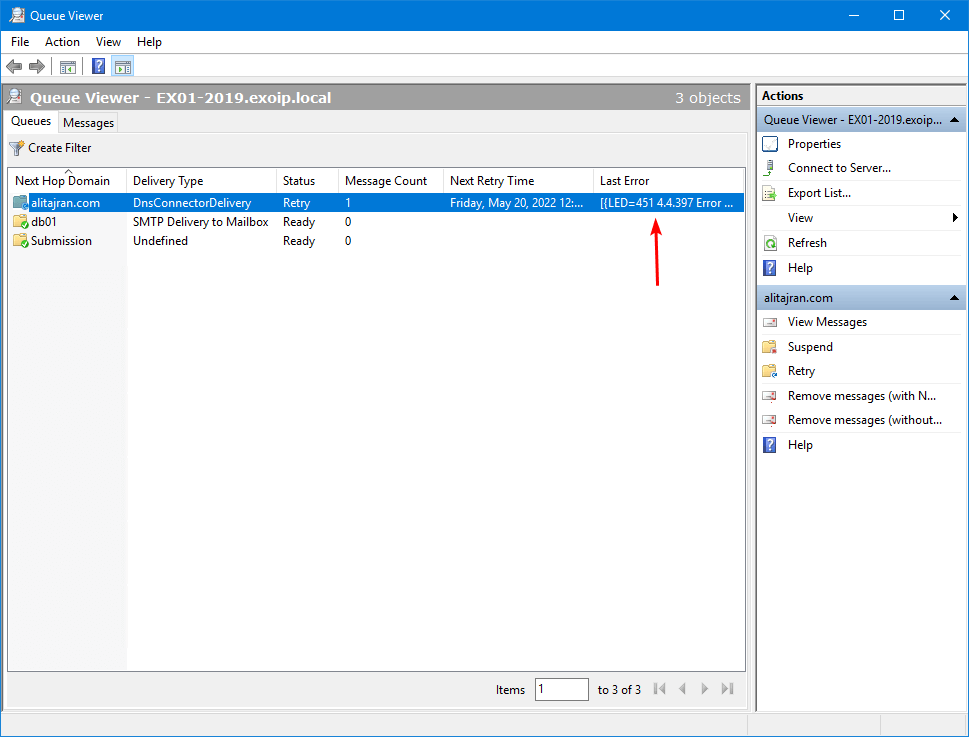
Find a message stuck in the mail queue. Next, read the Last Error message.
Note: Hover over the last error with your mouse to read the error message details.
In our example, a message is sent from an exoip.com mailbox to an www.alitajran.com mailbox.
A better way to get the last error is with PowerShell (Exchange Management Shell). Run the Get-Queue cmdlet to get the Exchange Server queues.
We can see that Identity EX01-2019\3 shows the Status retry.
[PS] C:\>Get-Queue
Identity DeliveryType Status MessageCount Velocity RiskLevel OutboundIPPool NextHopDomain
-------- ------------ ------ ------------ -------- --------- -------------- -------------
EX01-2019\3 DnsConnectorDelivery Retry 1 0 Normal 0 www.alitajran.com
EX01-2019\Submission Undefined Ready 0 0 Normal 0 SubmissionRun the Get-Queue cmdlet and include the identity from the previous step to get the error shown in the output.
[PS] C:\>Get-Queue -Identity "EX01-2019\3" | fl Identity,LastError
Identity : EX01-2019\3
LastError : [{LED=451 4.4.397 Error communicating with target host. -> 421 4.2.1 Unable to connect -> SocketTimedout:
Socket error code 10060};{MSG=};{FQDN=www.alitajran.com};{IP=104.47.18.74};{LRT=5/20/2022 12:04:13 PM}]The error is:
[{LED=451 4.4.397 Error communicating with target host. -> 421 4.2.1 Unable to connect -> SocketTimedout: Socket error code 10060};{MSG=};{FQDN=www.alitajran.com};{IP=104.47.18.74};{LRT=5/20/2022 12:04:13 PM}]
4.4.397 error communicating with target host 421 4.2.1 unable to connect
The 4.4.397 error communicating with target host 421 4.2.1 unable to connect is a generic error. You have to troubleshoot further why the error shows up as this can be different reasons:
- ISP blocks SMTP port 25
- Firewall blocks SMTP port 25
- Send connector misconfiguration
- Smart host offline
Solution for ISP blocks SMTP port 25
The solution is to use the route mail through smart hosts instead of the MX record associated with recipient domain option and another port than the default port 25 for outgoing mail in the send connector.
We will use the SpamBull spam filter for outgoing mail in this example.
This will not only send the mail through the smart host with port 587 to the outgoing world, but it will scan all the messages and filter unwanted mail from going out to the recipients, which is excellent.
And when we are at it, we will also configure the incoming messages through the SpamBull cloud-based spam filter. This way, the organization is also protected from incoming messages and not only outgoing ones.
This is the ultimate hygiene protection setup for incoming and outgoing messages.
Step 1. Check send connector
Check the Exchange Server send connector. Navigate to mail flow > send connectors. Select the send connector and click the edit icon in the toolbar.
The send connector is Internet email.
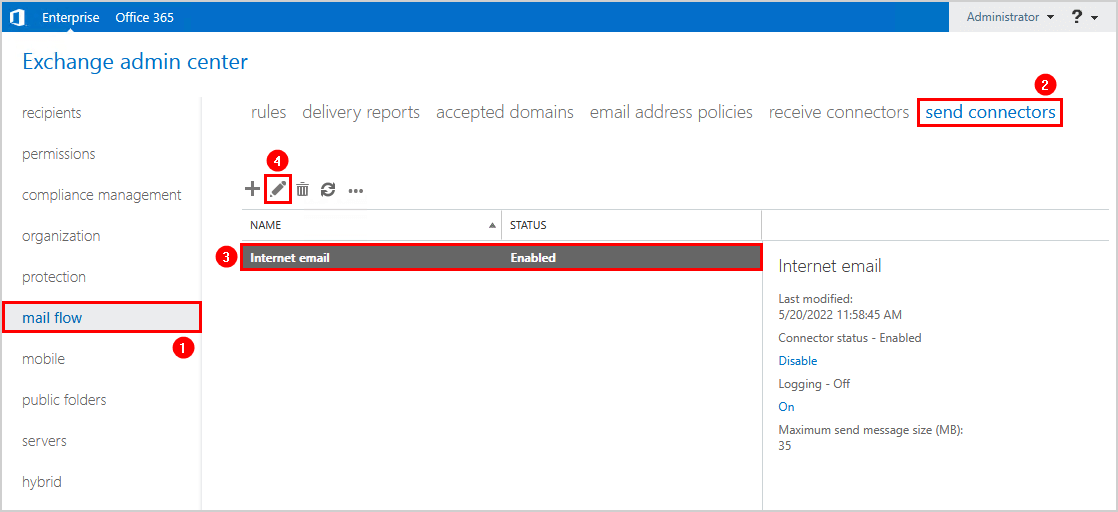
The send connector uses the option MX record associated with the recipient domain.
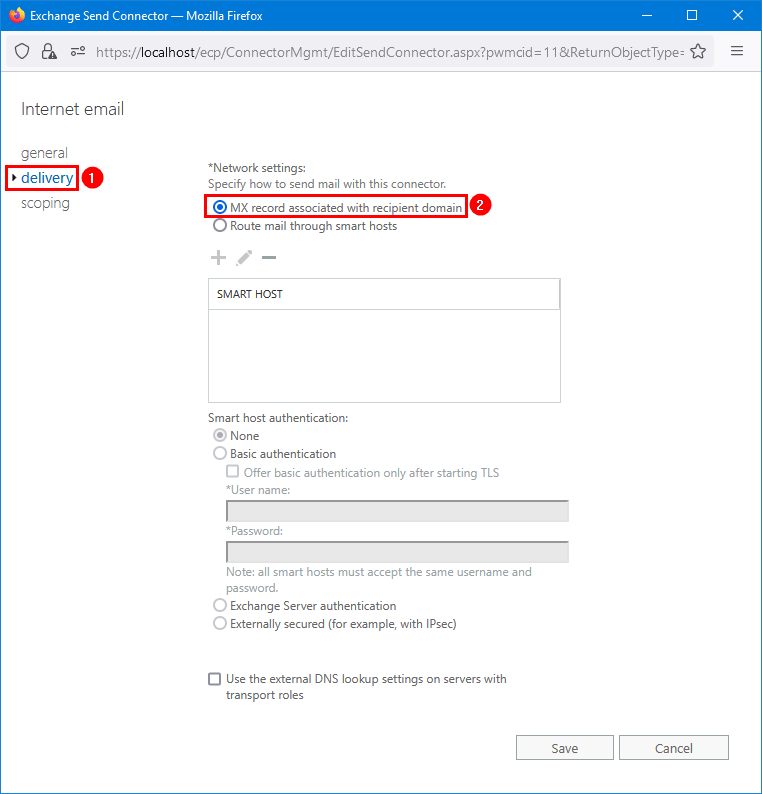
Step 2. Create new send connector
Create a new send connector SpamBullOut. Configure the send connector to route mail through the SpamBull spam filter as smart host.
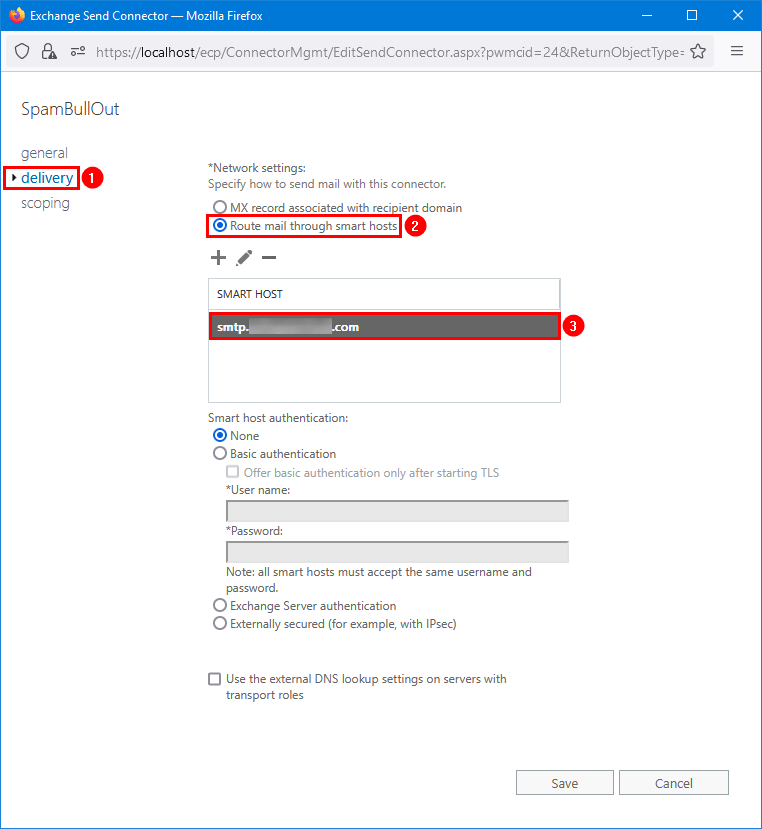
It’s important that you change the default port 25 to port 587. Configuring the port is only possible with Exchange Management Shell.
Note: Run Exchange Management Shell and set the new SpamBullOut send connector on port 587.
[PS] C:>Set-SendConnector -Identity "SpamBullOut" -Port:587Only allow port 587 from the source Exchange Server to the SpamBull spam filter in the firewall. Also, even though the ISP blocked port 25 from internal to external, I recommend blocking port 25 for everyone on LAN (internal) to WAN (outside world).
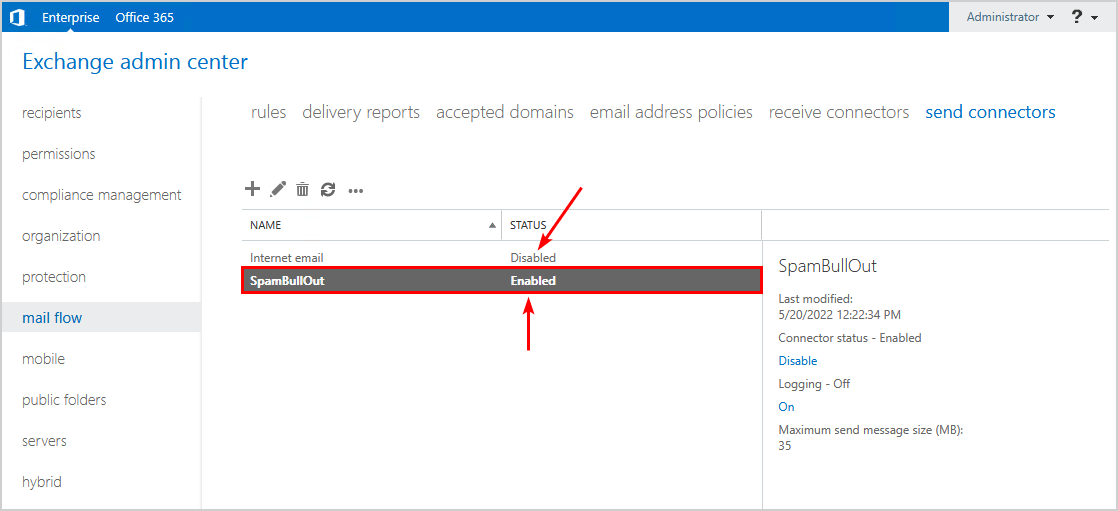
Step 3. Disable old send connector
Disable the old send connector. In this case, it’s the Internet email send connector.
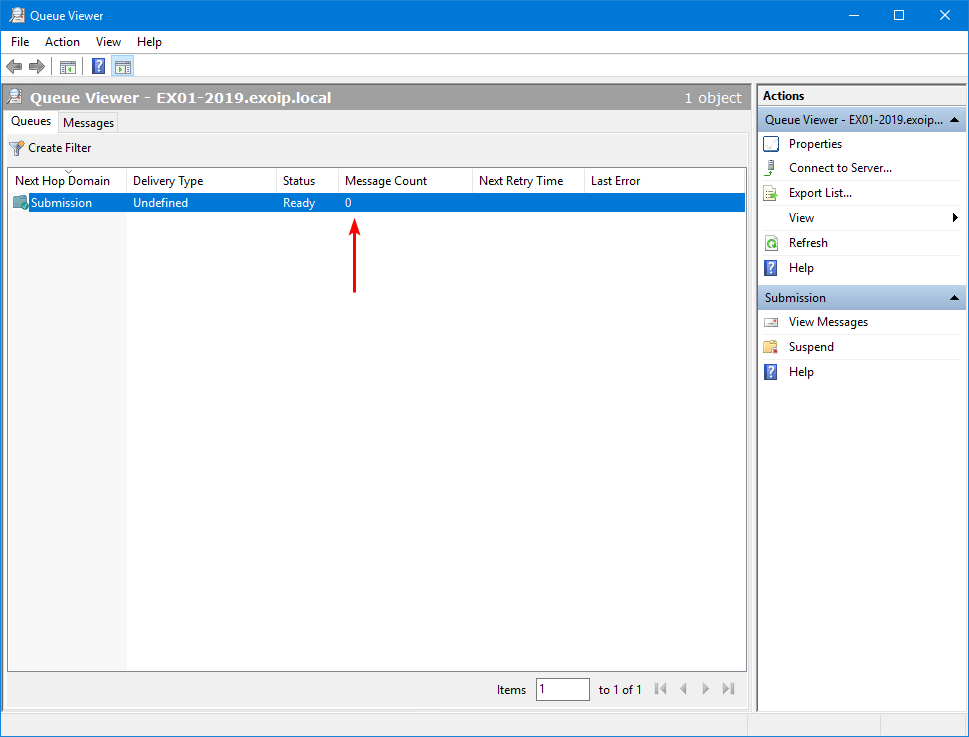
Step 4. Restart Microsoft Exchange Transport service
Restart the Microsoft Exchange Transport service.
[PS] C:\>Restart-Service MSExchangeTransportThe messages in the queue will start to process and become empty.
Check message header
Open the email that arrives at the recipient. Next, copy the message headers.
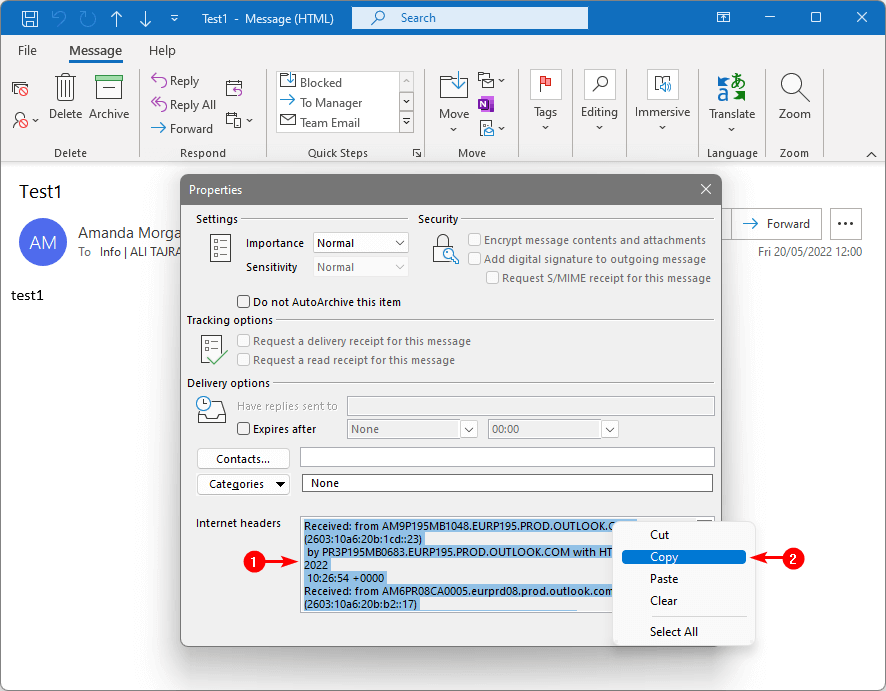
Go to Message Header Analyzer by Microsoft. Paste the copied message headers from the clipboard. Then, click on Analyze headers to check the hops.
The mailbox is hosted on a mailbox database in Exchange Server EX01-2019. The mail route went through Exchange EX01-2019 > SpamBull spam filter > Exchange Online.
Read more: Test outbound mail flow in Exchange Server »
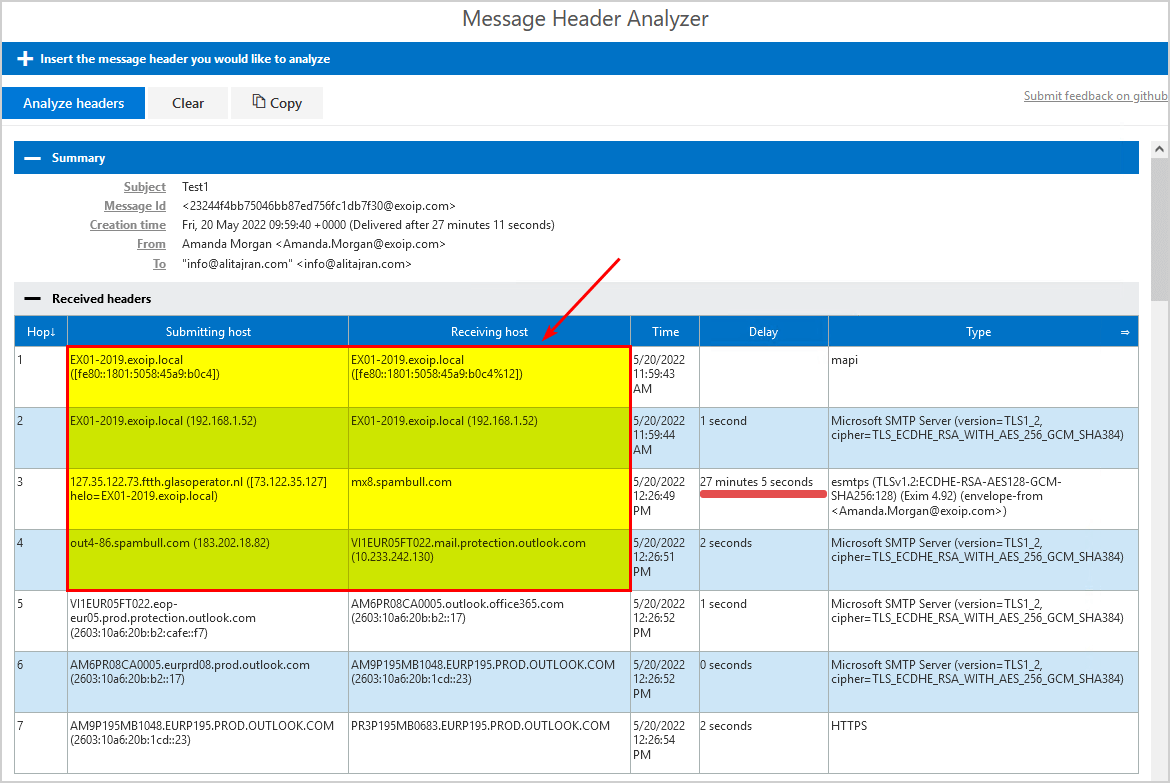
The message did take 27 minutes and 5 seconds. That’s because it stayed that much in the Exchange Server mail queue. It means that we identified the issue and implemented the SpamBull send connector within 30 minutes.
The internal IP and Exchange Server hostname show up by default in the message header. You would want to remove the message header in Exchange Server for security reasons.
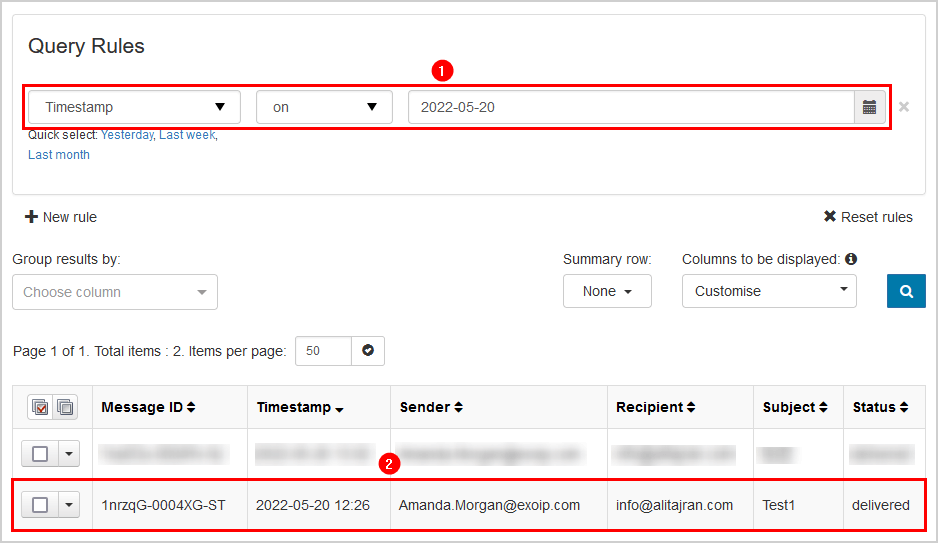
You can always check the outgoing logs in the SpamBull spam filter. Insert a timestamp and search for outgoing messages.
Why ISPs block port 25
Port 25 is the default port used to transport or communicate email across the Internet using the SMTP protocol. Many ISPs (Internet Service Providers) now block or restrict SMTP connections on port 25. The main reason for this is that when a computer gets infected by a virus, it can be hijacked by the virus writers to send out thousands, if not millions, of spam emails. So the ISPs have to prevent this from happening, and blocking the port is the only real solution.
All the ISPs will block port 25 on the WAN IP address eventually. It’s just a matter of time. If you have a business WAN IP, you might still use port 25. But, for how long till they end that service and block it? It’s better to prevent the error and implement a smart host with port 587 to have the outgoing mail flow up and running without frustrations and delays.
Keep reading: Stop Exchange Server sending spam »
Conclusion
You learned why the Exchange Server is unable to connect with the target host and send messages to external recipients. Many ISPs and firewall configurations now block outgoing mail/SMTP connections on port 25 (the default port for SMTP). That’s to stop spam from going out through their networks.
Suppose you have the SpamBull spam filter configured as a smart host and do not use port 25 for outgoing mail; you will not have this issue. I recommend blocking port 25 on the firewall and using port 587 for outgoing mail to keep everything secure without downtime.
Did you enjoy this article? You may also like Protect domain from spam, phishers and viruses. Don’t forget to follow us and share this article.


thank you for this! will this work if we have a hybrid server hosted on Azure VM? they are blocking port 25 for CSP and need to host a single mailbox on the hybrid server. All other mailboxes are already hosted in Exchange Online.
Currently there are the expected send and receive connectors between the 2 services.
It will work.
this issued happenes with outlook and office365 as well. so if we use smarthose from your product. it will work as well
It will work.