The time has come, the Exchange Server DAG (Database Availability Group) member failed, and it's…
Protect Exchange Server OWA/ECP from brute force attacks
A lot of bots attack the Exchange Server OWA and ECP page constantly. It’s the (security) engineers task to secure and protect the Exchange Server OWA/ECP URLs from attacks. Measures such as Multi-Factor Authentication (MFA) or only making the OWA/ECP accessible through VPN are excellent ideas. Another method to stop Exchange Server brute force attacks is integrating Google reCAPTCHA to the OWA/ECP page. It’s FREE and works excellently.
Table of contents
Protect Exchange Server OWA/ECP from attacks
There are a lot of methods to protect Exchange Server OWA/ECP from attacks. Here are the best ones to protect Exchange Server OWA/ECP from brute force attacks:
- Configure a third-party MFA solution
- Configure VPN so only users connected to the internal network can access Exchange OWA/ECP
- Enable selected countries only in the firewall that can access Exchange OWA/ECP
- Configure Azure app proxy (Azure AD Premium P1 or P2 license)
If you don’t want to spend money on an MFA solution or you don’t want to pay Azure AD Premium P1 or P2 license, you can protect Exchange OWA/ECP from brute force attacks by adding a reCAPTCHA in the sign-in page.
Exchange Server Google reCAPTCHA integration
To create a Google reCAPTCHA site and integrate it into Exchange Server OWA/ECP, go through the below steps:
Create Google reCAPTCHA site
The first step is to create a new Google reCAPTCHA site. Once we have the reCAPTCHA keys, we can integrate them into Exchange Server.
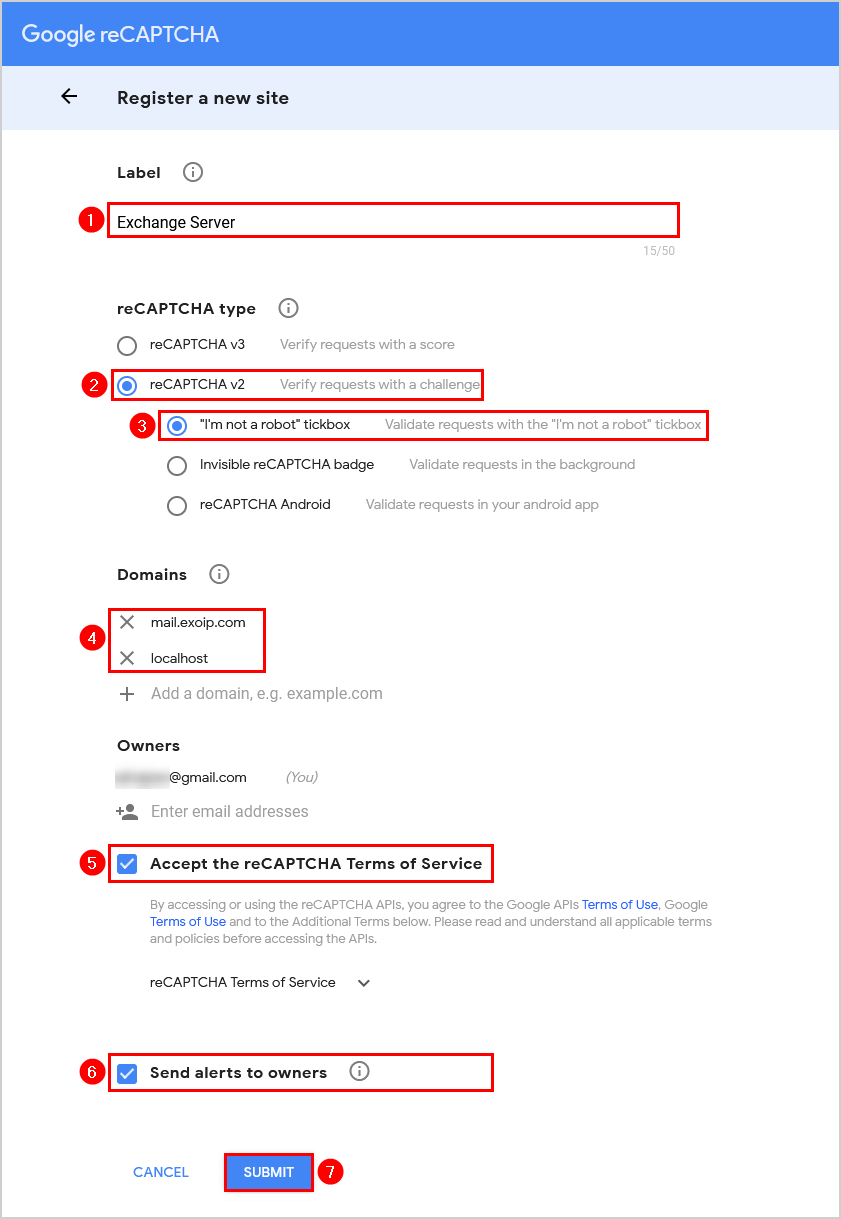
Sign in to Google reCAPTCHA and fill in the below details:
- Label: Exchange Server
- reCAPTCHA type: reCAPTCHA v2 – “I’m not a robot” tickbox
- Domains: mail.exoip.com (your Exchange URL) and localhost
Check both the checkboxes:
- Accept the reCAPTCHA Terms of Service
- Send alerts to owners
Click on Submit.
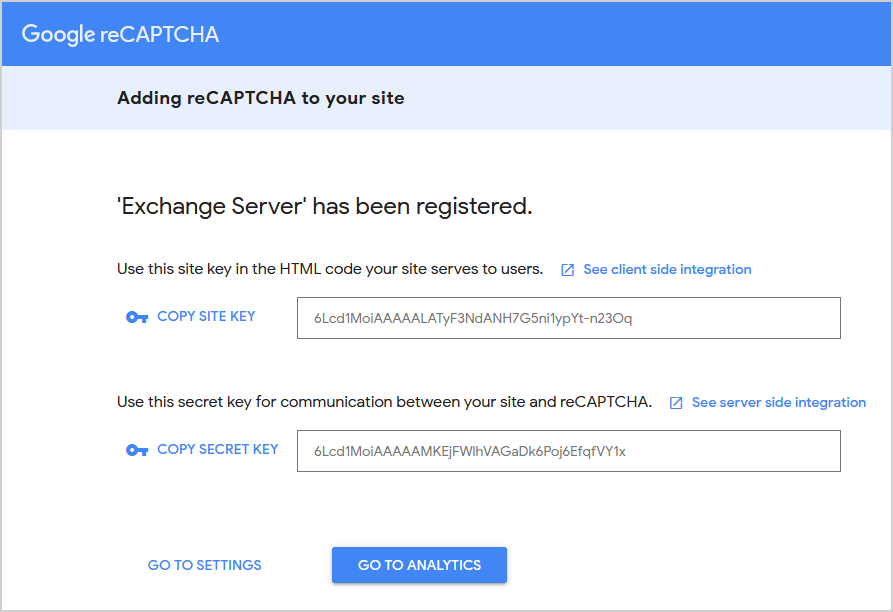
The site key and secret key will appear. Copy both keys and save them because you need them in the next step.
Create Exchange Server reCAPTCHA page
Let’s integrate the site key into Exchange Server.
Note: Do the below steps on every Exchange Server (CAS).
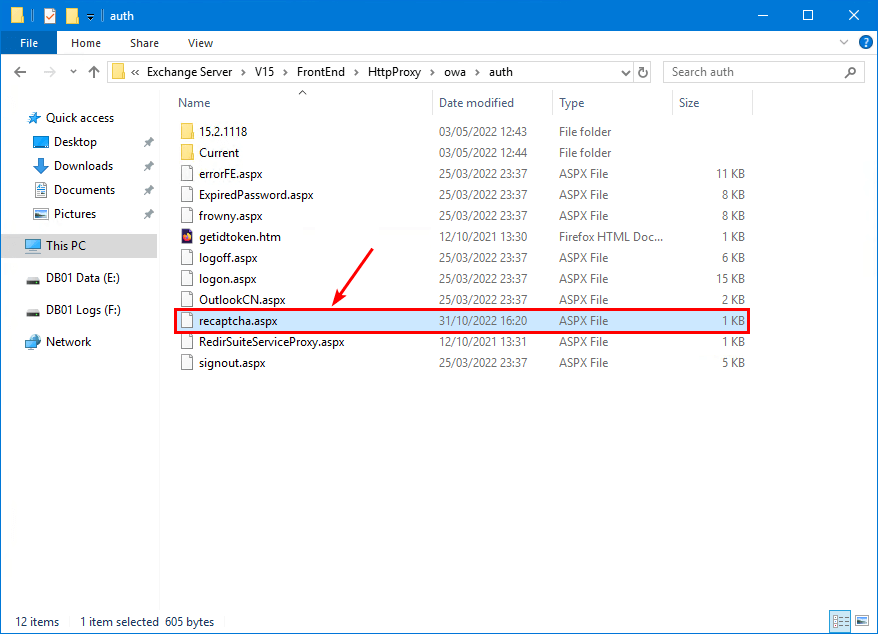
Sign in to the Exchange Server and go to the below path. Suppose you have an older Exchange Server version, change V15 to another version. For example, V14.
C:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\authCreate a new file with Notepad with the name recaptcha.aspx in that folder.
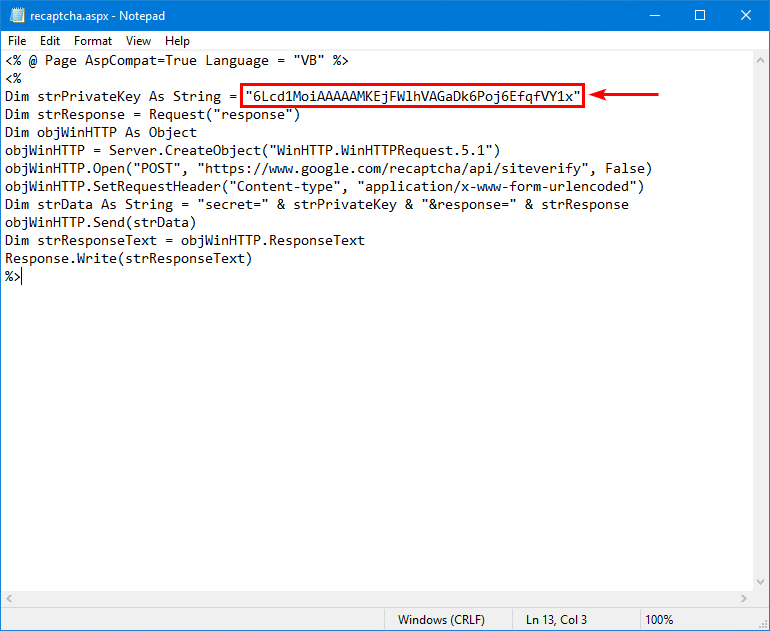
Copy/paste the below information into it.
<% @ Page AspCompat=True Language = "VB" %>
<%
Dim strPrivateKey As String = "SECRET_KEY"
Dim strResponse = Request("response")
Dim objWinHTTP As Object
objWinHTTP = Server.CreateObject("WinHTTP.WinHTTPRequest.5.1")
objWinHTTP.Open("POST", "https://www.google.com/recaptcha/api/siteverify", False)
objWinHTTP.SetRequestHeader("Content-type", "application/x-www-form-urlencoded")
Dim strData As String = "secret=" & strPrivateKey & "&response=" & strResponse
objWinHTTP.Send(strData)
Dim strResponseText = objWinHTTP.ResponseText
Response.Write(strResponseText)
%>Paste the Google reCAPTCHA secret key you copied in the previous step and paste it in the field SECRET_KEY.
Configure Exchange Server OWA/ECP logon page
Let’s integrate the secret key into Exchange Server.
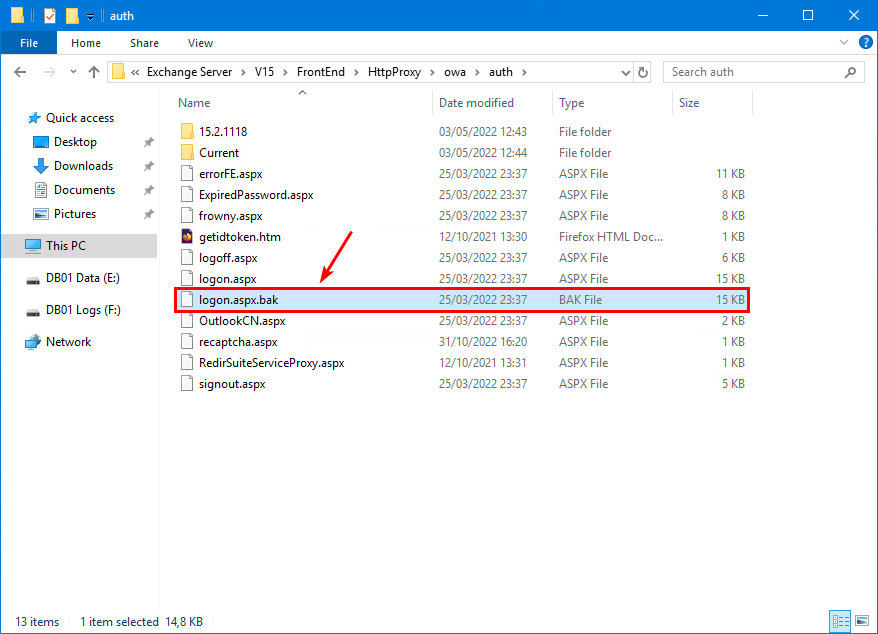
Make a backup of the logon.aspx file, just in case you have to revert the changes. Copy logon.aspx and rename it to logon.aspx.bak.
Note: The file logon.aspx will be rewritten to its original state when you install Exchange Server CU. So write down in your manual to replace the file after the CU and test that the Google reCAPTCHA works.
Open the logon.aspx file with Notepad and modify the below:
Find:
<form action="/owa/auth.owa"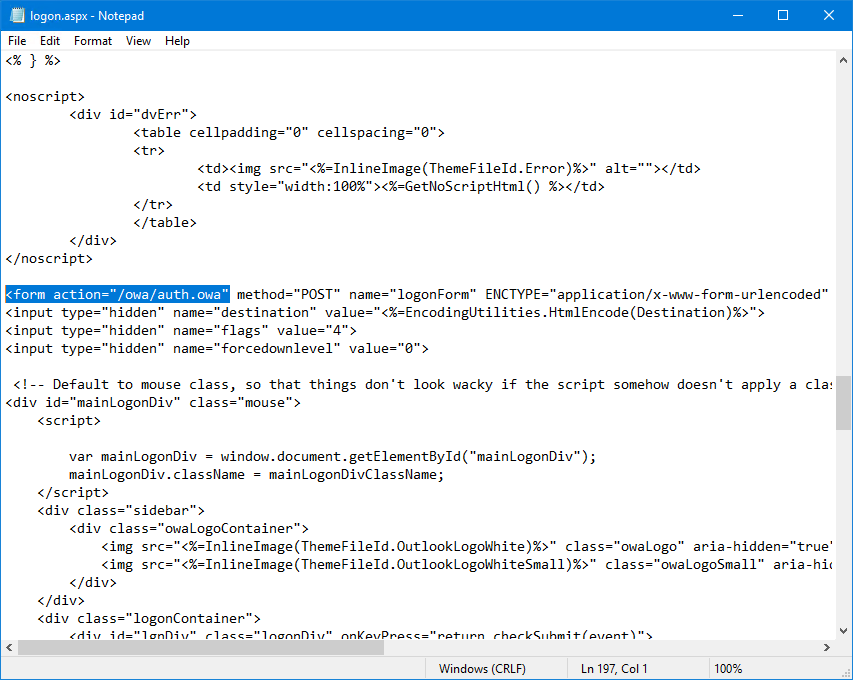
Change to:
<form action=""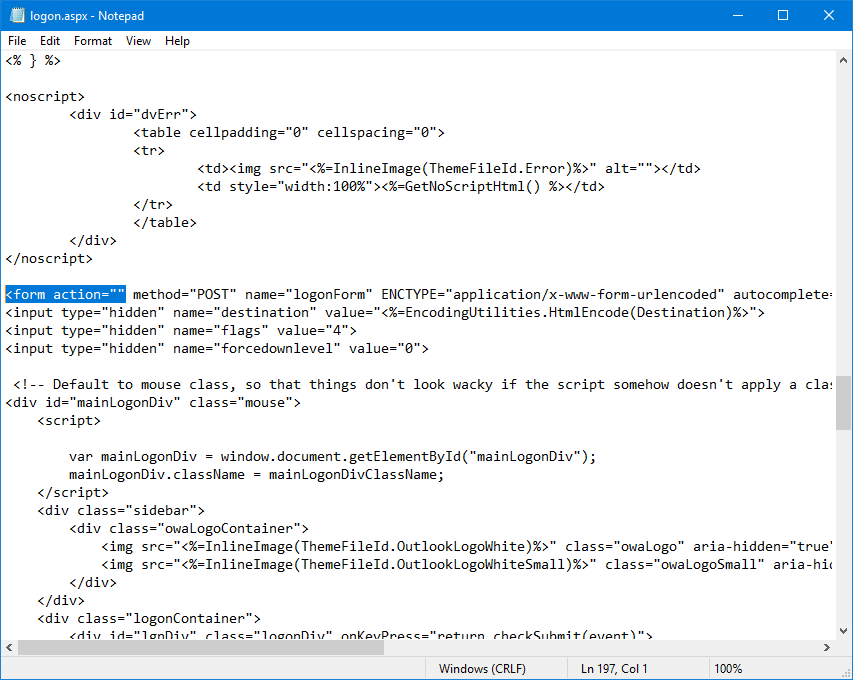
Find:
<div onclick="clkLgn()"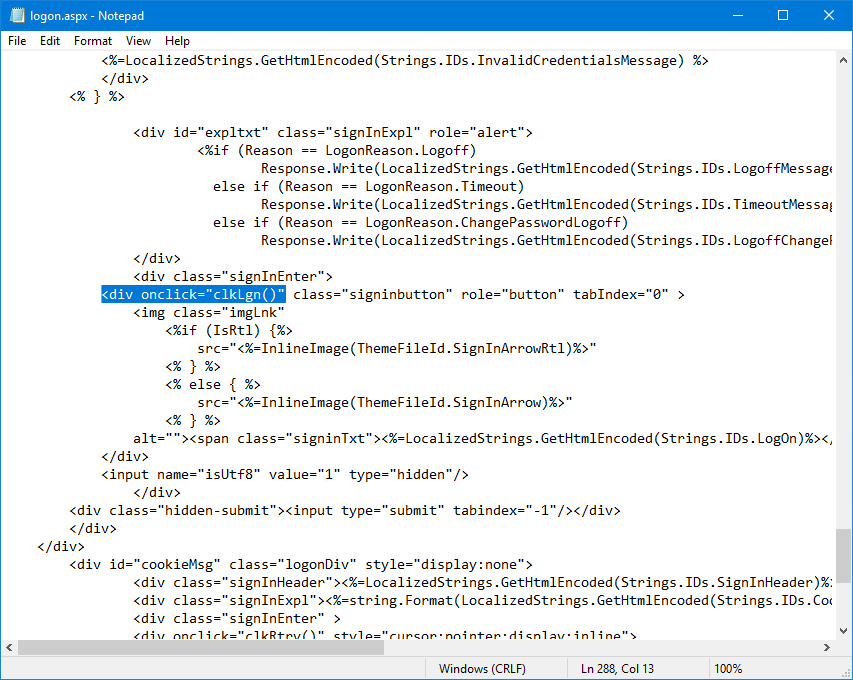
Change to:
<div onclick="myClkLgn()"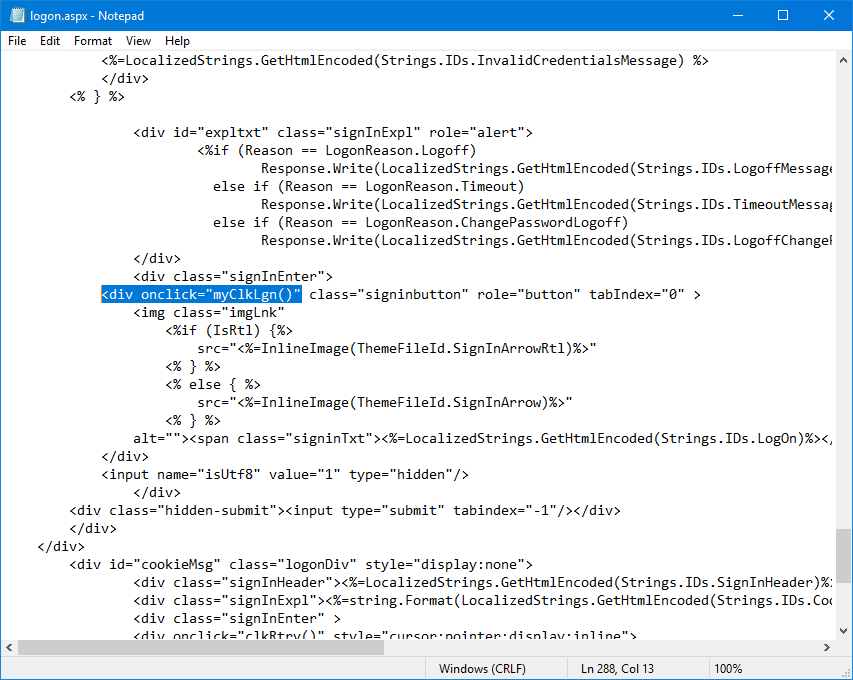
Find:
<div><input id="passwordText"Next, press the Enter button and create a couple of empty lines.
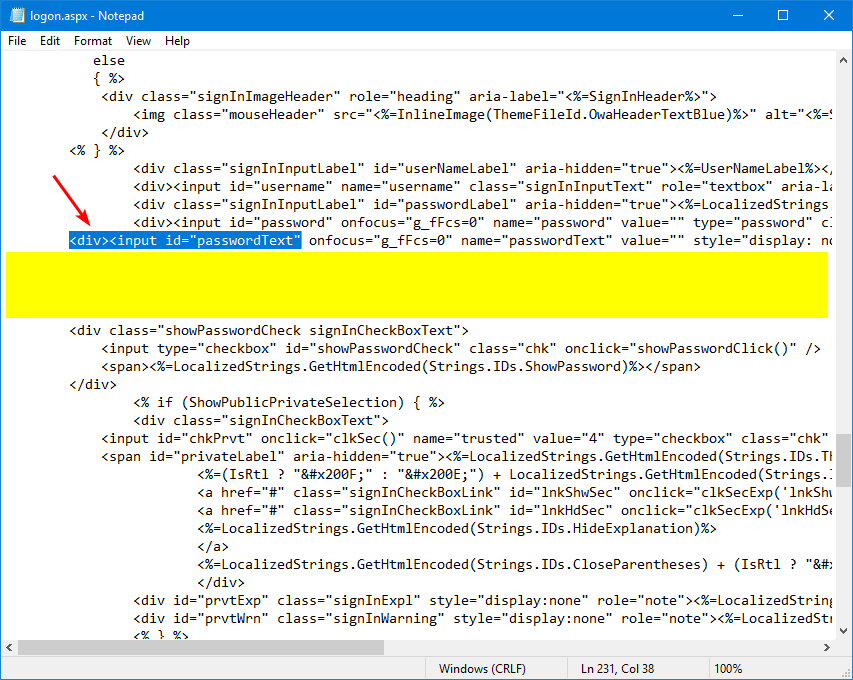
Copy/paste the below information into the empty lines.
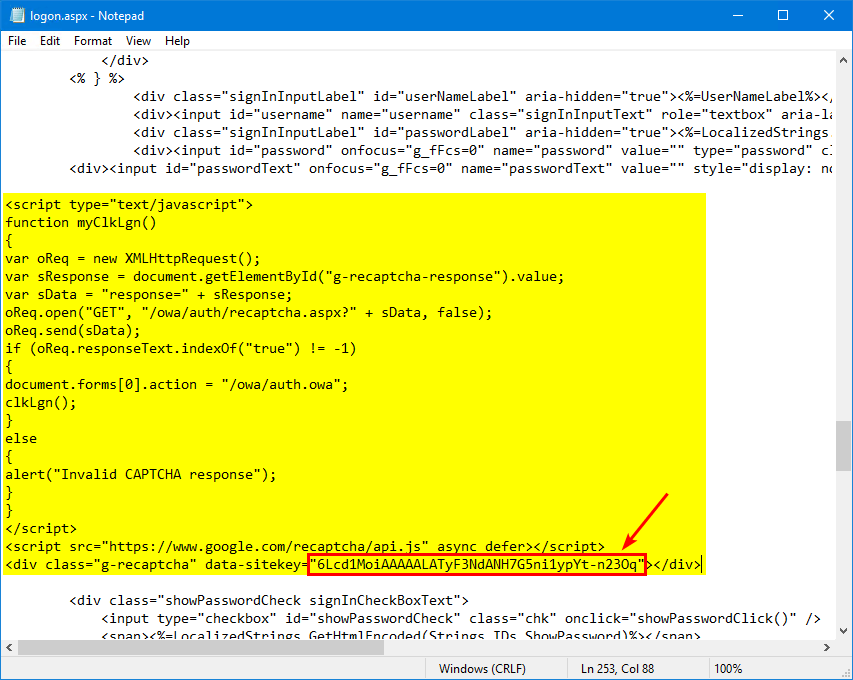
<script type="text/javascript">
function myClkLgn()
{
var oReq = new XMLHttpRequest();
var sResponse = document.getElementById("g-recaptcha-response").value;
var sData = "response=" + sResponse;
oReq.open("GET", "/owa/auth/recaptcha.aspx?" + sData, false);
oReq.send(sData);
if (oReq.responseText.indexOf("true") != -1)
{
document.forms[0].action = "/owa/auth.owa";
clkLgn();
}
else
{
alert("Invalid CAPTCHA response");
}
}
</script>
<script src="https://www.google.com/recaptcha/api.js" async defer></script>
<div class="g-recaptcha" data-sitekey="SITE_KEY"></div>Paste the Google reCAPTCHA site key you copied in the previous step and paste it in the field SITE_KEY.
Restart IIS on Exchange Server
You don’t need to restart IIS on the Exchange Server, and the Google reCAPTCHA will immediately appear on the Exchange Server OWA/ECP page.
Suppose it doesn’t, start Command Prompt as administrator and restart Internet Information Services (IIS) on the Exchange Server.
iisresetVerify Exchange Server OWA/ECP with Google reCAPTCHA
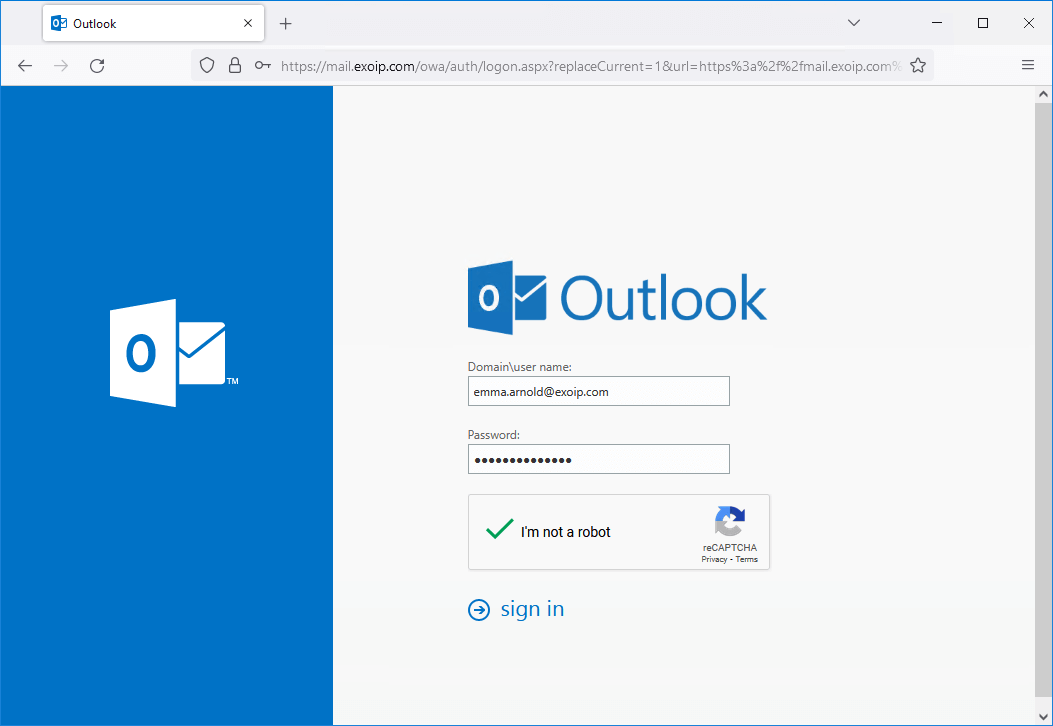
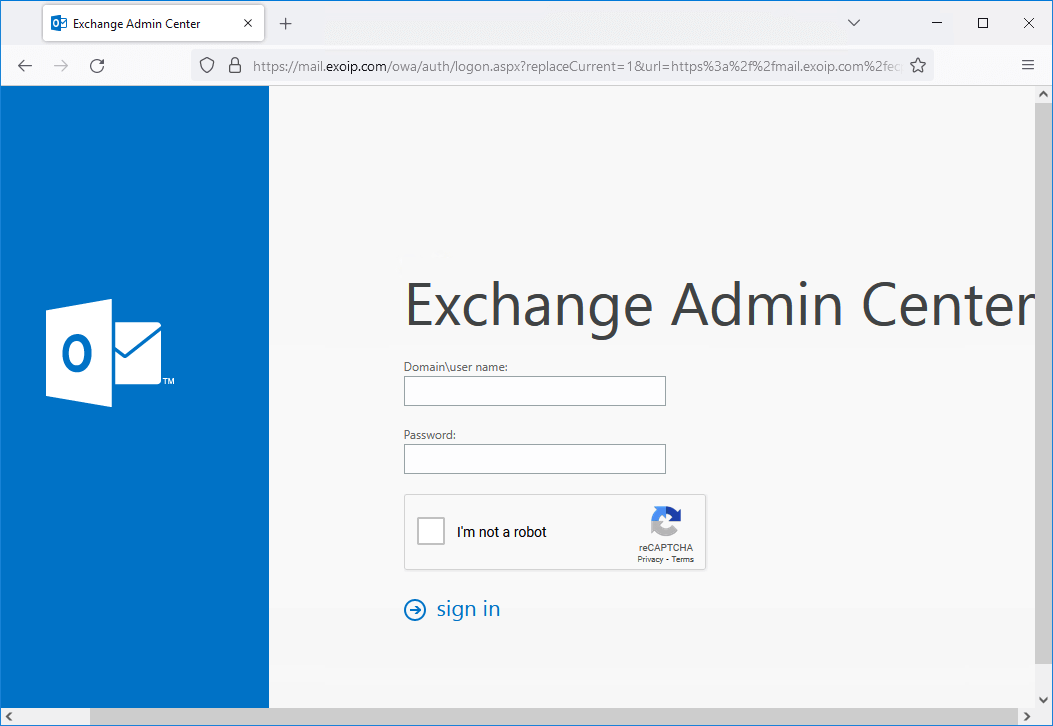
Start your favorite web browser and go to the Exchange Server OWA address.
The Google reCAPTCHA is visible.
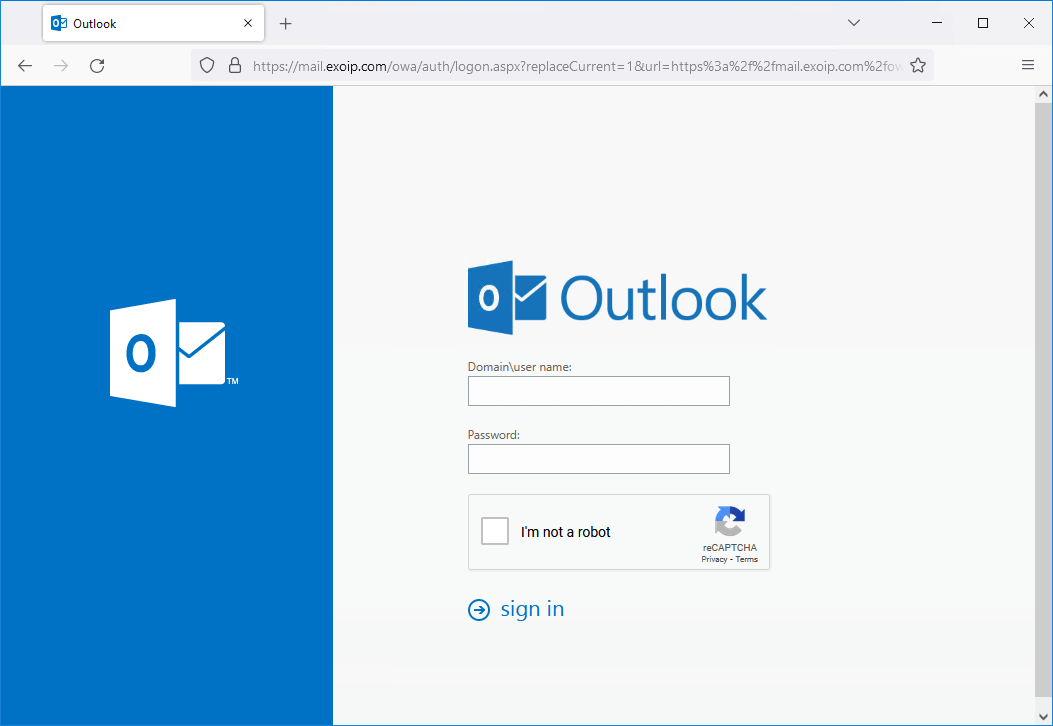
Fill in the user credentials and check the Google reCAPTCHA checkbox. Next, click on Sign in.
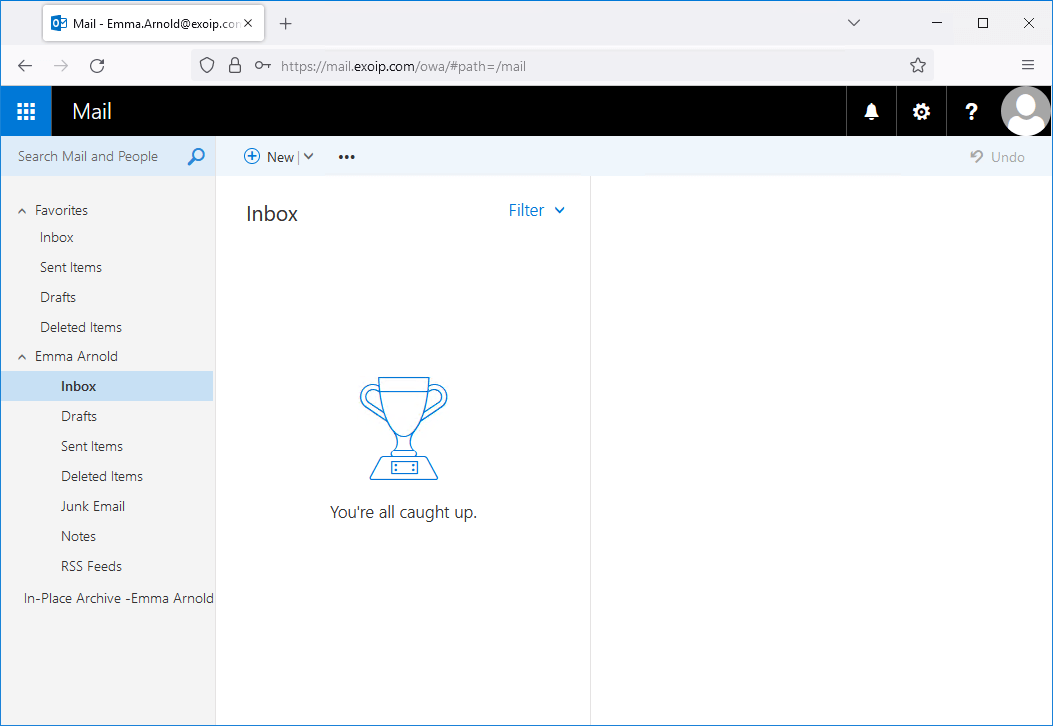
The user will successfully sign in.
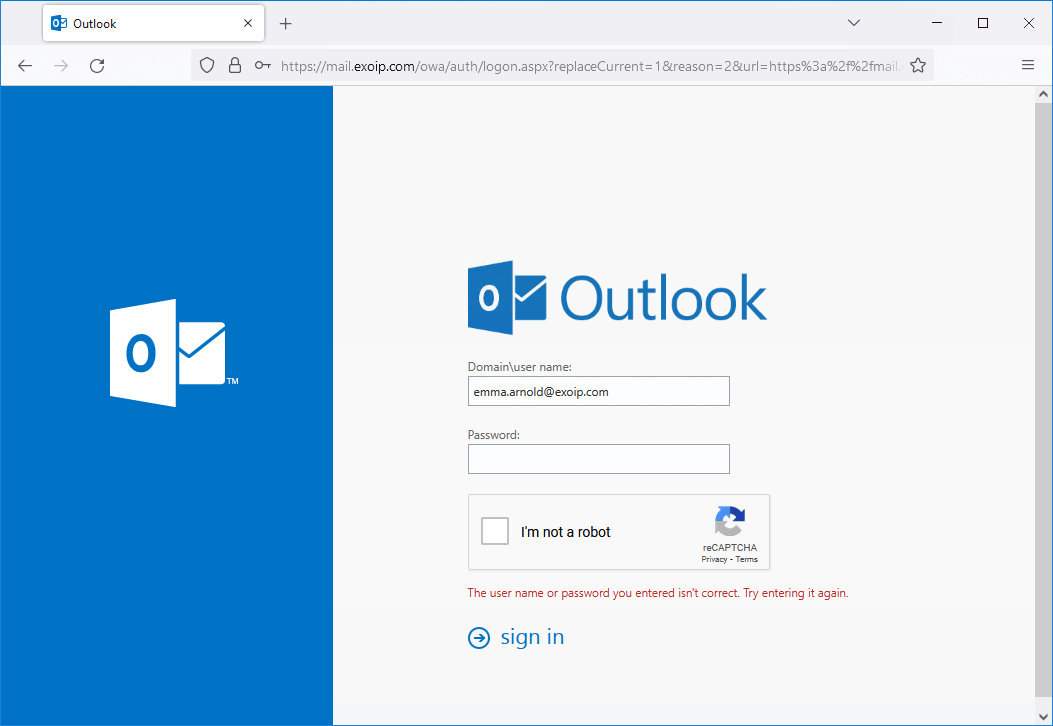
If the user fills in the wrong credentials, it will show the standard message: The user name or password you entered isn’t correct. Try entering it again.
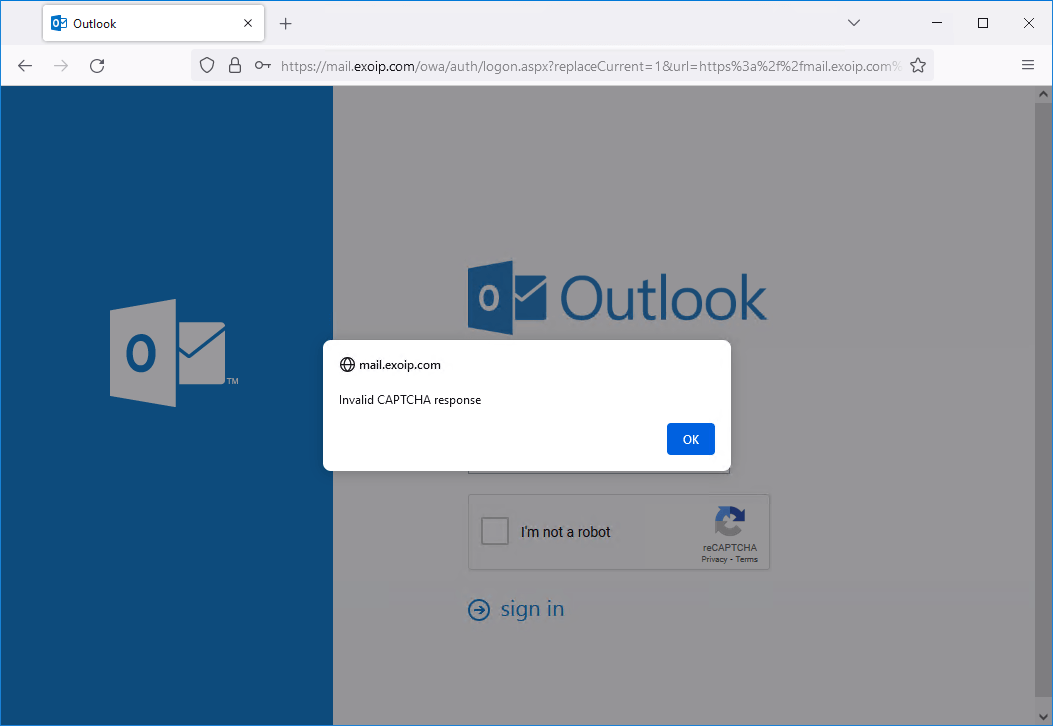
Suppose the user doesn’t accept the Google reCAPTCHA box and clicks on sign in. A message will appear with text: Invalid CAPTCHA response.
The same applies to the Exchange Admin Center (ECP) page.
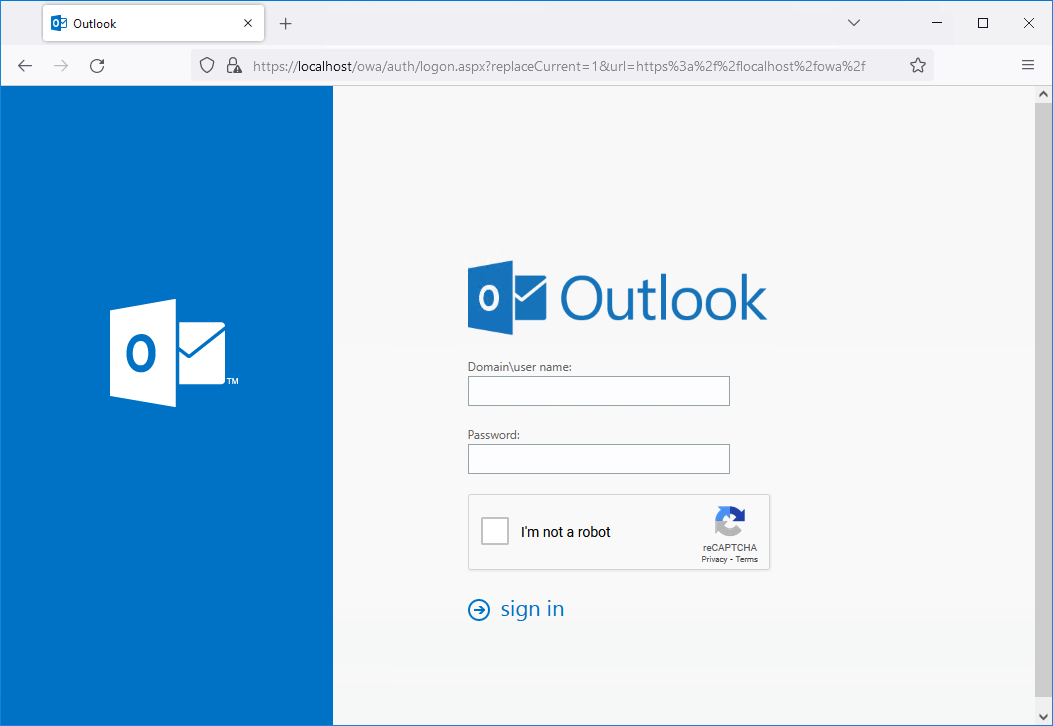
It will also work when browsing to https://localhost/owa or https://localhost/ecp. That’s because you did add localhost in the first step when creating the site in Google reCAPTCHA.
That’s it!
Read more: Secure Active Directory passwords from breaches »
Conclusion
You learned how to protect Exchange Server OWA/ECP from brute force attacks. First, create a free Google reCAPTCHA. After that, adjust the Exchange Server file so it will display and use the Google reCAPTCHA box on the OWA/ECP page. Combine this with an MFA solution, and you are good to go.
Did you enjoy this article? You may also like Disable external access to ECP in Exchange Server. Don’t forget to follow us and share this article.


Working well
how i can apply authenticator like google or Microsoft or any on OWA , thanks
I made the changes to exchange and it worked first try, thank you for the info. However, I get the following warning in the Captcha admin panel.
We detected that your site is verifying reCAPTCHA passed solutions less than 50% of the time. This could indicate a problem with your integration with reCAPTCHA.
Any idea how to fix this?
Hello Group
Does anyone have this working again on Exchange 2019 CU13? It could be me, but after re-applying the changes to the login page it down not appear to work.
Thanks
Andrew
I tested it on Exchange Server 2019 CU13, and it still works.
I modified the code that it will not require a captcha for localhost (‘Exchange Admin Center’ at https://localhost/ecp/).
Instead of changeing the code like described by Ali, you always use a “if not localhost else clause”.
Can you post what you changed for this? Would also like to work it like this.
Thanx
thank you for this guide, but this doesn’t help me against MSExchangeFrontEndTransport id 1035 bruteforce attacks i guess this is not what i expected is for
Thank you so much! I was able to implement this successfully.The only issue I have is that many a time, when I click sign in after I have checked recaptcha, the login refuses to progress.It will stand still, having clicked on sign in severally.Though it progresses at times when I switch between browsers but not always. What can I try to resolve this please?
I have two exchange servers (2016) with common name xxx.yyyy.com like https://xxx.yyyy.com/owa
I am running Exchange 2019 and seeing the same problems – clicking ‘Sign In’ and nothing happens
Hello Ali,
Thank you for all the great articles, i have the Captcha setup. it shows it and i am able to click to verify it. But after that entering my user id and password nothing happens. No error no message. Do you know what could be the issue?
Hi Ali, The internet access of my Exchange servers is closed. In this case, does “recaptcha” work?
Will Firewall be given access permission from Servers to the Google services?
If so, if my internet connection is cut in the company, does it mean that I cannot connect to OWA/ECP even on the inner network?
In this case, I will have to change the name of the logon.aspx file (with “recaptcha” codes) and leave the original logon.aspx.bak file again by making “logon.aspx”. Does it make sense?
Thank you
Good day.
And what about the cost from Google? Can I install this for free, on a private account? Or do I need some kind of enterprise solution?
You can use a private Google account, and it’s FREE.
Great article Ali,
Does this all break when installing the next CU?
Thanks,
Ase
Yes, it does remove the Google reCAPTCHA configuration when you install Exchange Server CU.
I added a note to the article and explained what would be overwritten.
Hi Ali,
Not able to get it working, only receive “Verification expired. Check the checkbox again” after a long wait after pressing sign-in.
Localhost for ECP is not working either.
When registering domains at google, should I register:
mysite.com or the actual I use mail.mysite.com?
Thanks,
Ase
You should add the domains:
1. mail.mysite.com (your Exchange URL)
2. localhost
Awesome! Thank you, is that works on remote desktop services too? :p
Thank You Ali!
Is the reCAPTCHA Version 3 also compatible with your modifications?
No, it’s not.
Will there be a problem connecting to the Exchange server from remote Outlook clients accessing the message over HTTPS?
After an Exchange CU or SU these changes to the logon.aspx might be gone right?
Yes, it does remove the Google reCAPTCHA configuration when you install Exchange Server CU. But the configuration is kept when you install Exchange Server SU.
I added a note to the article and explained what would be overwritten.
Hi,
I have a Exchange 2019 with DAG. I want to install reCAPTCHA. Will I have problems with installation?
There should be no issues that occur, and if there are, it’s easy to roll back the changes.
thank your answer. I created Google reCaptcha in Owa. I marked reCaptcha. I write my password. But I can’t enter. why could it be ?