It's best to use Conditional Access based MFA when you have Microsoft Entra ID P1…
DKIM selector2 not working for Microsoft 365 domain
We did add a domain to the Microsoft 365 tenant and enabled DKIM for that specific domain. While checking the DKIM records (selector1 and selector2), the result shows that no DKIM record found for the selector2 record. Why is the DKIM selector2 not working? In this article, you will learn how to fix no DKIM record found for selector2.
Table of contents
No DKIM record found for selector2
We did add a domain to the Microsoft 365 admin portal and configured DKIM for that domain.
Let’s check both the DKIM selector records with MxToolbox:
- Selector1 record
- Selector2 record
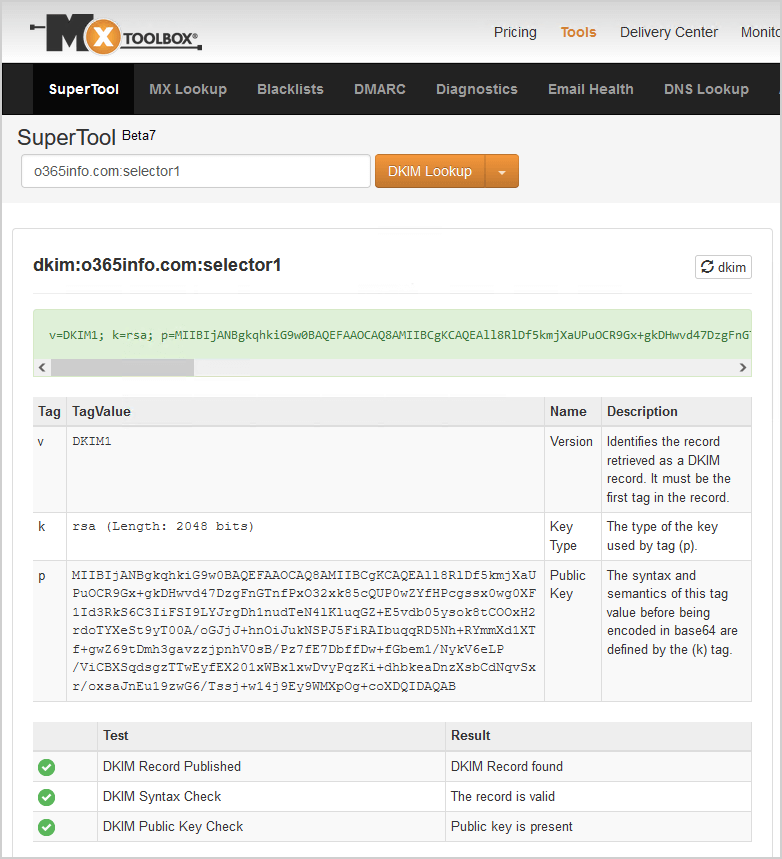
DKIM selector1 record
The DKIM selector1 in DNS shows that the record is published.
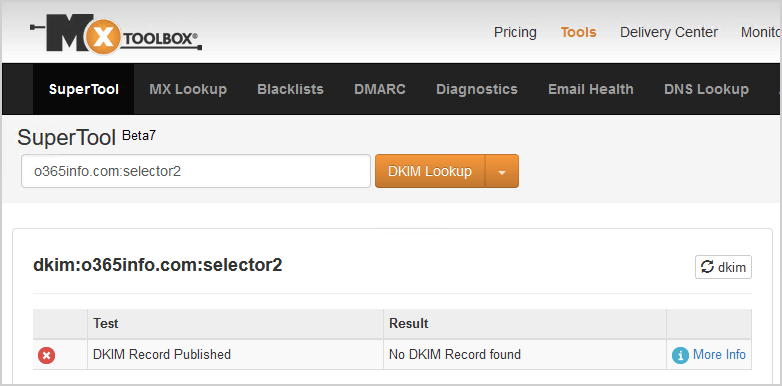
DKIM selector2 record
The DKIM selector2 in DNS shows No DKIM Record found.
Solution to no DKIM record found for selector2
The solution for No DKIM record found for selector2 is to rotate the domain’s DKIM keys:
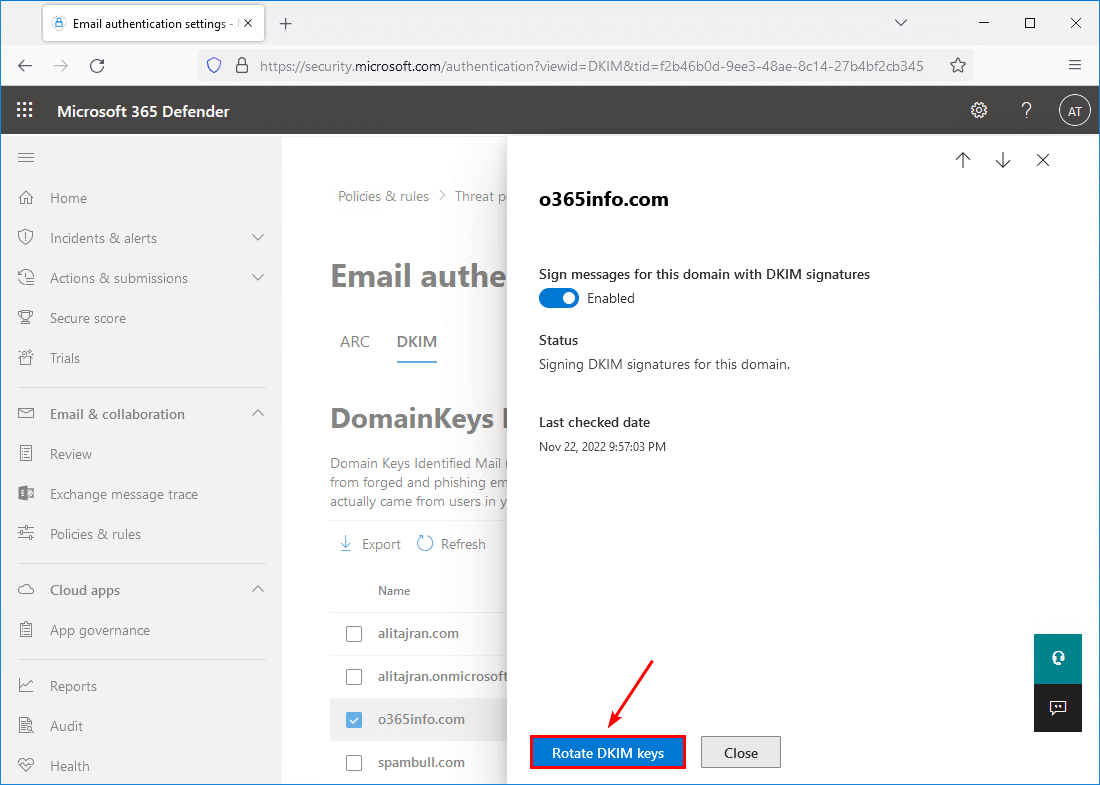
- Go to the Microsoft 365 DKIM page
- Select the domain in the list
- Click on Rotate DKIM keys
- Verify that the status shows Rotating keys for this domain and signing DKIM signatures
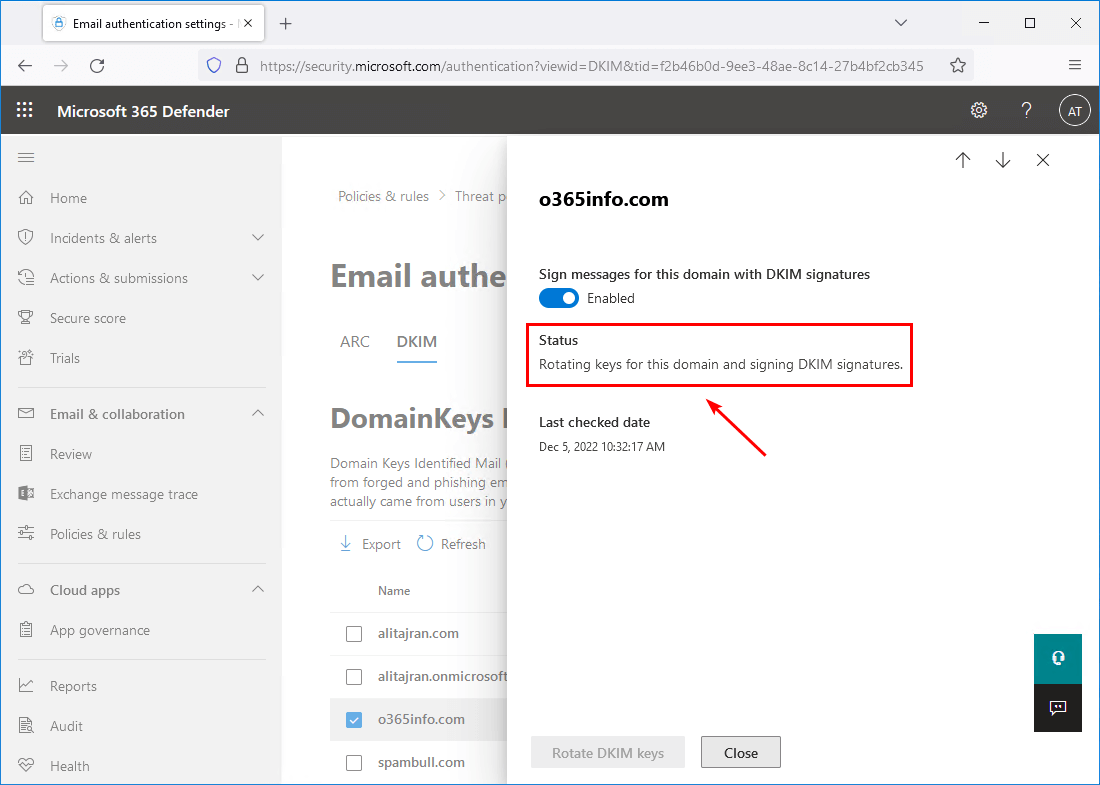
In the next step, we will check that the DKIM selector2 record is valid and that the public key is present.
Verify DKIM selector2 record works
Go to MxToolbox and verify the DKIM selector2 record. The DKIM record is available and shown.
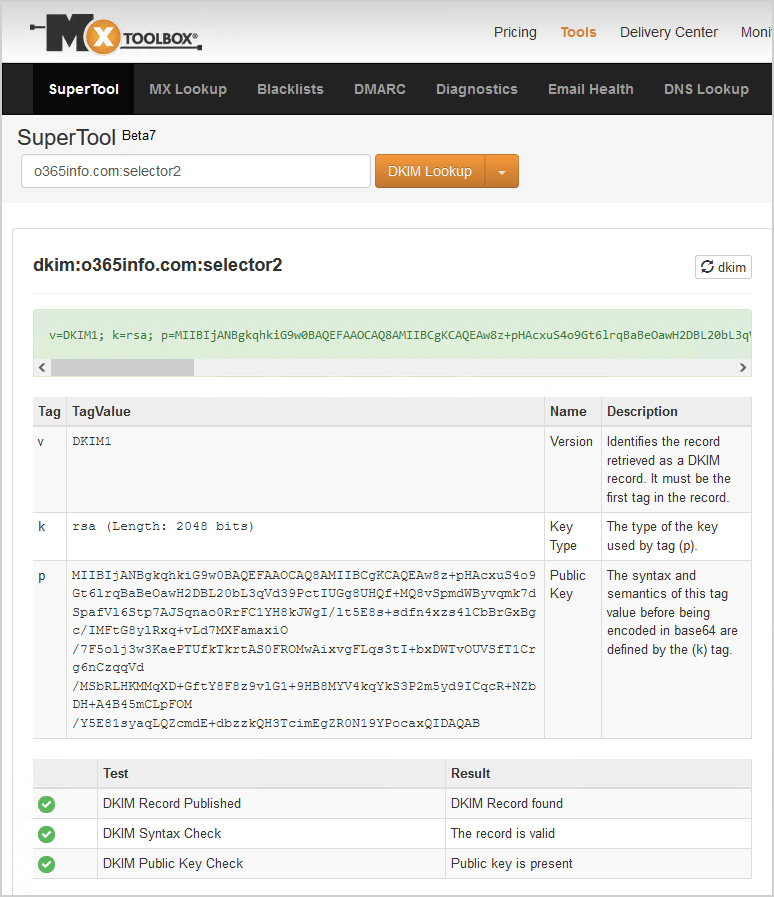
Everything looks great!
Read more: Protect domain from spam, phishers and viruses »
Conclusion
You learned how to fix no DKIM record found for selector2. The solution is to rotate the DKIM keys for the domain in Microsoft 365 portal. Then, give it a few minutes and verify that the selector2 record is found and published.
Did you enjoy this article? You may also like How to configure enhanced filtering for connectors (skip listing). Don’t forget to follow us and share this article.



I had the same issue. after rotating, selector1 is 1024 bits, however selector2 becomes 2048bits. is this ok ?
thank you for your solution.
Oliver
I have a different issue. I can get to the Email authentication settings page in Defender, I click on DKIM, I see two accepted domains. I click the check box for my domain and…nothing! No popup, nothing. Just sits there. I have popups enabled. What am I doing wrong?
I tried the following:
1) Rotate the keys + wait till status of rotation completes.
2) Turn off DKIM and turn it back up after some time.
2) Turn off DKIM, remove DNS records, wait till no selectors are working, put DNS records back, turn DKIM back.
Nothing worked so far, only selector 1 is working. Trying to contact support now.
Fantastic! this was causing me “fail-unaligned” on DKIM/DMARC alignment on all emails going through Selector2. rotating the keys solved it. same error appears on other DMARC clients, so it looks like you have to rotate after initial setup! thanks!
Worked a treat – thanks! Had exactly the issue of selector1 looking OK but selector2 not showing up. Did a quick rotation and a minute later both check out fine on MXToolbox ????
This is a good article that talks about a real actual problem. I found it while searching for a solution for myself.
But I find the part that says “Then, give it a few minutes and verify that the selector2 record is found and published.” to be very unrealistic since it’s taking me hours and it still says “Status Rotating keys for this domain and signing DKIM signatures.”
From googling a bit I can see many others are reporting the same, including someone saying it took them a week!
What should we expect? Can you give update the article with a more reasonable estimate ?
Don’t look at the DKIM status in Microsoft 365 Defender portal. But check the results in MxToolbox after you rotate the DKIM keys.
Give it 1-5 minutes (a few minutes) and check the DKIM selector2 record in MxToolbox. If it still doesn’t appear, something else is happening.
Defender portal is still saying Rotating keys for this domain and signing DKIM signatures.
Mxtoolbox is still saying “No DKIM Record found” for selector 2. But selector 1 is detected fine.
I dont understand whats going on 🙁
Hi
I just checked again and finally, its saying
> Status
> Signing DKIM signatures for this domain.
But… selector 2 is still not detected by mxtoolbox and easydmarc dot com ! 🙁
Good news update! 🙂
I had a flashback of something similar happening in the past and how I think I solved it. So, I went to the Security admin center (aka M365 defender portal) and disabled DKIM on the custom domain. And then enabled it again.
Immediately after that, it started showing correctly on Mxtoolbox and Easydmarc’s DKIM Record Checker.
I suggest you add this simple approach to your article.
Hello,
thanks for the article.
I added the DNS zones but there is only one selector that appears. Selector 2 does not appear.
When I want to activate “sign messages for this domain with DKIM signatures” I get a client error saying that the CNAMES records are missing.
As long as the option is not activated, I cannot perform a key rotation.
Do you have an idea? I have already recreated the CNAME several times at our host.
Thanks for your help.
Have a look at the article Configure DKIM record for Office 365. It might take an hour or more before the DNS changes are updated across the Internet.
Thanks for the feedback,
I have already configured and checked the CNAME at the hosting company about 10 times.
I only have the selector1 that appears. I think there must be a problem on the Microsoft side. Some people have already encountered the problem on the net.
If someone has a solution or a workaround before opening a support ticket at Microsoft I would be delighted!
Is the missing selector likely to cause any specific issues?
Yes, DKIM authentication will fail for outgoing mail.
It can negatively impact deliverability, as mailbox providers may send the message to the spam folder or block it entirely.
When the email hits the receiving server, the server looks at the email headers to find the “s=selector2” tag. If the tag is present, the server extracts the selector from the tag, then looks up the DNS for the public key at the following location:
selector2._domainkey.yourdomain.com
If the public key is found, the server uses it to decrypt the message to check its integrity. If the check passes, DKIM authentication succeeds; otherwise, it fails.