You created a batch to migrate the mailboxes from Exchange On-Premises to Exchange Online. Normally…
Outlook needs password after Hybrid Modern Authentication implementation
Hybrid Modern Authentication (HMA) is implemented in the on-premises organization. This way, the users with an on-premises mailbox will use modern authentication instead of basic authentication. It’s great because from now on, they will use Microsoft Entra ID Conditional Access policies. One of these policies is Multi-Factor Authentication (MFA).
After the HMA implementation, the users can’t connect to Outlook. Some users see that Outlook asks for their password, and some users get the modern authentication sign-in prompt. After they sign in with their credentials, an error shows up. In this article, you will learn why this is happening, and the solution for Outlook asks for the password after configuring Hybrid Modern Authentication.
Table of contents
What is happening?
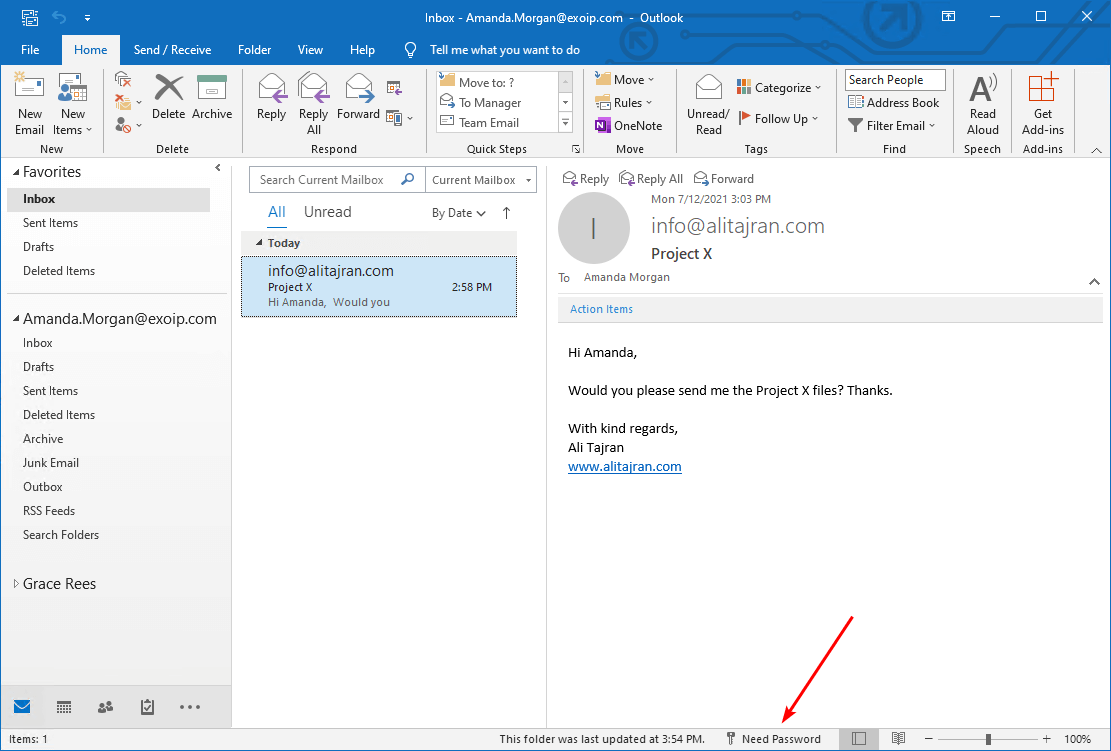
We have the user Amanda, which has an on-premises mailbox. She can sign in to Outlook, and the mail shows up. Everything works great with basic authentication. However, after configuring Hybrid Modern Authentication and restarting Outlook, Outlook shows that it needs a password.
Let’s remove and create a new Outlook profile for Amanda. After doing that, we get the error: CAA2000B.
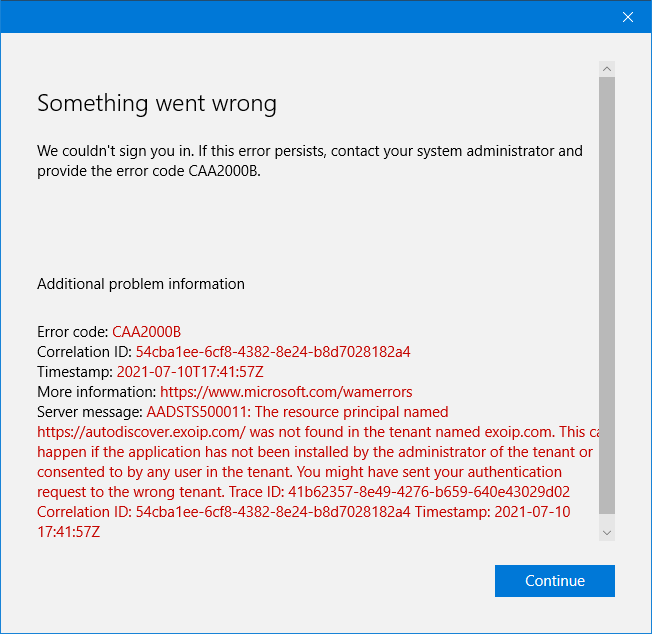
Something went wrong
We couldn’t sign you in. If this error persists, contact your system administrator and provide the error code CAA2000B.
Additional problem information
Error code: CAA200B
Correlation ID: 54cba1ee-6cf8-4382-8e24-b8d7028182a4
Timestamp: 2021-07-10T17:45:57Z
More information: https://www.microsoft.com/wamerrors
Server message: AADSTS500011: The resource principal named http://autodiscover.exoip.com/ was not found in the tenant named exoip.com. This can happen if the application has not been installed by the administrator of the tenant or consented to by any user in the tenant. You might have sent your authentication request to the wrong tenant.
Why do we see the error code CAA2000B, and why is it showing that Outlook needs password? What is the solution for these issues after configuring Hybrid Modern Authentication?
Solution for Outlook needs password after Hybrid Modern Authentication implementation
The solution is to get the Exchange virtual directory URLs. After that, add the on-premises web service URLs as SPNs (Service Principal Name). Let’s have a look at how to do that.
Step 1. Get virtual directory URLs
Start Exchange Management Shell as administrator on your Exchange Server on-premises. Run the four cmdlets to retrieve the virtual directory URLs.
Get-MapiVirtualDirectory | fl server,*url*
Get-WebServicesVirtualDirectory | fl server,*url*
Get-ClientAccessServer | fl Name, AutodiscoverServiceInternalUri
Get-OABVirtualDirectory | fl server,*url*The results appear in the output below after running every command. Make a note of all the internal and external URLs because you will need to add these URLs in one of the next steps.
In our example, we have the same name for internal and external URLs. We recommend configuring it like this as it will simplify a lot. If you didn’t, you would see internal addresses that end with .local or .lan in the output.
# Get-MapiVirtualDirectory | fl server,*url*
Server : EX01-2016
InternalUrl : https://mail.exoip.com/mapi
ExternalUrl : https://mail.exoip.com/mapi
Server : EX02-2016
InternalUrl : https://mail.exoip.com/mapi
ExternalUrl : https://mail.exoip.com/mapi
# Get-WebServicesVirtualDirectory | fl server,*url*
Server : EX01-2016
InternalNLBBypassUrl :
InternalUrl : https://mail.exoip.com/EWS/Exchange.asmx
ExternalUrl : https://mail.exoip.com/EWS/Exchange.asmx
Server : EX02-2016
InternalNLBBypassUrl :
InternalUrl : https://mail.exoip.com/EWS/Exchange.asmx
ExternalUrl : https://mail.exoip.com/EWS/Exchange.asmx
# Get-ClientAccessServer | fl Name, AutodiscoverServiceInternalUri
WARNING: The Get-ClientAccessServer cmdlet will be removed in a future version of Exchange. Use the
Get-ClientAccessService cmdlet instead. If you have any scripts that use the Get-ClientAccessServer cmdlet, update them
to use the Get-ClientAccessService cmdlet. For more information, see http://go.microsoft.com/fwlink/p/?LinkId=254711.
Name : EX01-2016
AutoDiscoverServiceInternalUri : https://autodiscover.exoip.com/Autodiscover/Autodiscover.xml
Name : EX02-2016
AutoDiscoverServiceInternalUri : https://autodiscover.exoip.com/Autodiscover/Autodiscover.xml
# Get-OABVirtualDirectory | fl server,*url*
Server : EX01-2016
InternalUrl : https://mail.exoip.com/OAB
ExternalUrl : https://mail.exoip.com/OAB
Server : EX02-2016
InternalUrl : https://mail.exoip.com/OAB
ExternalUrl : https://mail.exoip.com/OABStep 2. Get Exchange related SPNs
Run PowerShell as administrator and connect to Microsoft Graph PowerShell. Sign in with your Microsoft 365 global administrator credentials.
Connect-MgGraph -Scopes "Application.Read.All", "Application.ReadWrite.All"Run the Get-MgServicePrincipal cmdlet to get the Exchange related URLs in the cloud for the application 00000002-0000-0ff1-ce00-000000000000.
Get-MgServicePrincipal -Filter "AppId eq '00000002-0000-0ff1-ce00-000000000000'" | select -ExpandProperty ServicePrincipalNamesTake note of (and screenshot for later comparison) the output of this command, which should include an https://autodiscover.yourdomain.com and https://mail.yourdomain.com URL, but mostly consist of SPNs that begin with 00000002-0000-0ff1-ce00-000000000000/.
00000002-0000-0ff1-ce00-000000000000/mail.exoip.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.M365x877334.mail.onmicrosoft.com
00000002-0000-0ff1-ce00-000000000000/M365x877334.mail.onmicrosoft.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.exoip.com
00000002-0000-0ff1-ce00-000000000000/exoip.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.exoip.local
00000002-0000-0ff1-ce00-000000000000/exoip.local
00000002-0000-0ff1-ce00-000000000000/outlook.office365.com
00000002-0000-0ff1-ce00-000000000000/mail.office365.com
00000002-0000-0ff1-ce00-000000000000/outlook.com
00000002-0000-0ff1-ce00-000000000000/*.outlook.com
00000002-0000-0ff1-ce00-000000000000
https://ps.compliance.protection.outlook.com
https://outlook-sdf.office.com/
https://outlook-sdf.office365.com/
https://outlook.office365.com:443/
https://outlook.office.com/
https://outlook.office365.com/
https://outlook.com/
https://ps.protection.outlook.com/
https://outlook-tdf.office.com/
https://outlook-tdf-2.office.com/
https://ps.outlook.comMost likely, the https:// URLs from your on-premises are missing. Therefore, we will need to add those specific records to this list in the next step.
Step 3. Add on-premises web service URLs as SPNs
If you don’t see your internal and external MAPI/HTTP, EWS, ActiveSync, OAB, and Autodiscover records in this list, you must add them using the command below in Microsoft Graph PowerShell.
In this example, the URLs are https://mail.exoip.com/ and https://autodiscover.exoip.com/. Replace the URLs with your own.
$x = Get-MgServicePrincipal -Filter "AppId eq '00000002-0000-0ff1-ce00-000000000000'"
$ServicePrincipalUpdate = @(
"https://mail.exoip.com/",
"https://autodiscover.exoip.com/"
)
Update-MgServicePrincipal -ServicePrincipalId $x.Id -ServicePrincipalNames $ServicePrincipalUpdateStep 4. Verify Exchange related SPNs
Verify that you added the new records by running the Get-MgServicePrincipal cmdlet in Microsoft Graph PowerShell.
Get-MgServicePrincipal -Filter "AppId eq '00000002-0000-0ff1-ce00-000000000000'" | select -ExpandProperty ServicePrincipalNamesLook through the output. Compare the before list/screenshot against the new list of SPNs. You might also take a screenshot of the new list for your records. If you were successful, you would see the two new URLs in the list.
Going by our example, the list of SPNs will now include the specific URLs https://mail.exoip.com/ and https://autodiscover.exoip.com/. See it at the top of the list.
https://autodiscover.exoip.com/
https://mail.exoip.com/
00000002-0000-0ff1-ce00-000000000000/mail.exoip.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.M365x877334.mail.onmicrosoft.com
00000002-0000-0ff1-ce00-000000000000/M365x877334.mail.onmicrosoft.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.exoip.com
00000002-0000-0ff1-ce00-000000000000/exoip.com
00000002-0000-0ff1-ce00-000000000000/autodiscover.exoip.local
00000002-0000-0ff1-ce00-000000000000/exoip.local
00000002-0000-0ff1-ce00-000000000000/outlook.office365.com
00000002-0000-0ff1-ce00-000000000000/mail.office365.com
00000002-0000-0ff1-ce00-000000000000/outlook.com
00000002-0000-0ff1-ce00-000000000000/*.outlook.com
00000002-0000-0ff1-ce00-000000000000
https://ps.compliance.protection.outlook.com
https://outlook-sdf.office.com/
https://outlook-sdf.office365.com/
https://outlook.office365.com:443/
https://outlook.office.com/
https://outlook.office365.com/
https://outlook.com/
https://ps.protection.outlook.com/
https://outlook-tdf.office.com/
https://outlook-tdf-2.office.com/
https://ps.outlook.comVerify your work
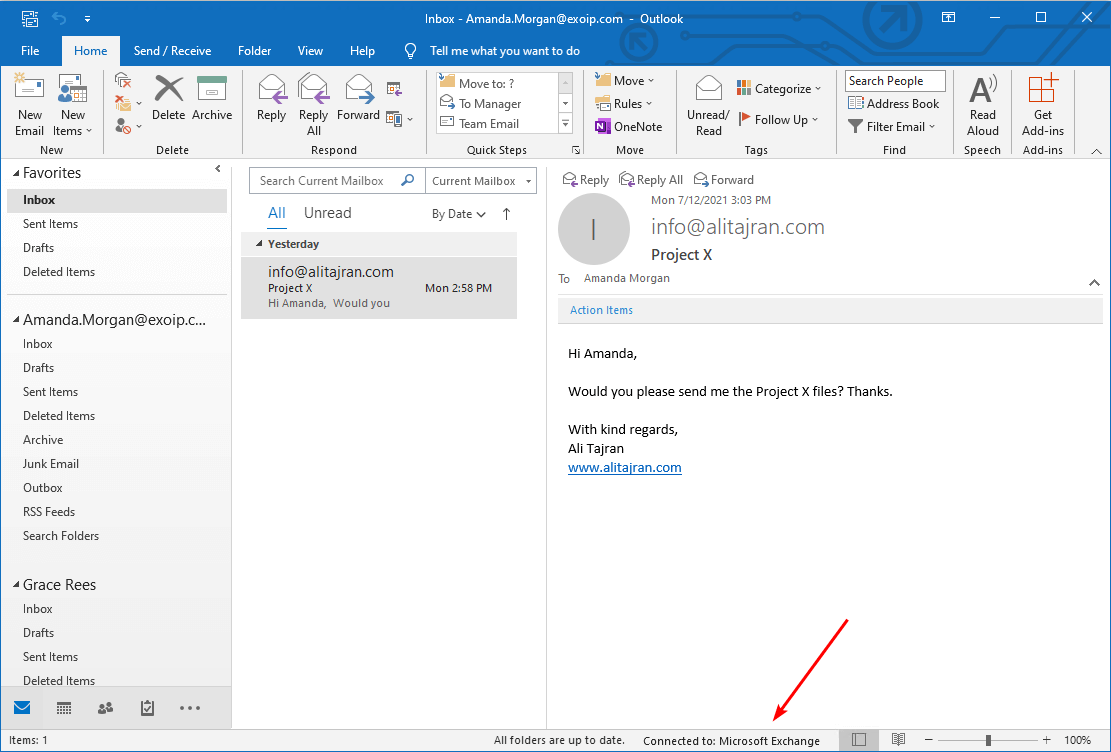
Restart Outlook, and you will see in the bottom bar that it’s connected to: Microsoft Exchange.
That’s it!
If that didn’t work for you, you might have other configurations you didn’t set up correctly when configuring Hybrid Modern Authentication. We recommend you go through the article Configure Hybrid Modern Authentication in Exchange on-premises. It explains every detail step by step on how to implement Hybrid Modern Authentication.
Conclusion
You learned why Outlook shows the message Need Password after Hybrid Modern Authentication implementation. First, get the Exchange on-premises virtual directory URLs. After that, add the virtual directory URLs as SPNs. Finally, restart Outlook, and it will show that it’s connected to Microsoft Exchange.
Did you enjoy this article? You may also like Outlook prompts for password after migration to Office 365. Don’t forget to follow us and share this article.


Hello,
Thanks for this article, i’ve configured the Hybrid Modern Wizard in minimal Exchange 2013 OnPrem and after that , i’ve the password prompt on Outlook for OnPrem mailbox.
i’ve only Internal URL and just External URL for the EWS, but it’s not work in classical hybrid.
could you confirm to me that i can add the Internal URL in the config to solve my issues ?
Actually, i’ve re run the hybrid Wiazrd and setup in classical wit Some error . and i’ve disabled OAuth on Virtual directoy OnPrem, the issus still existe